A hacking collective widely believed to be backed by the Iranian government, operating under the moniker "Handala," recently asserted responsibility for infiltrating the personal email account of Kash Patel, a prominent former U.S. government official. This alleged cyberattack marks a significant development in the ongoing digital skirmishes between state-sponsored actors and raises critical questions about the security of personal data belonging to individuals with access to sensitive national information.
Allegations Surface in Geopolitical Cyber Conflict
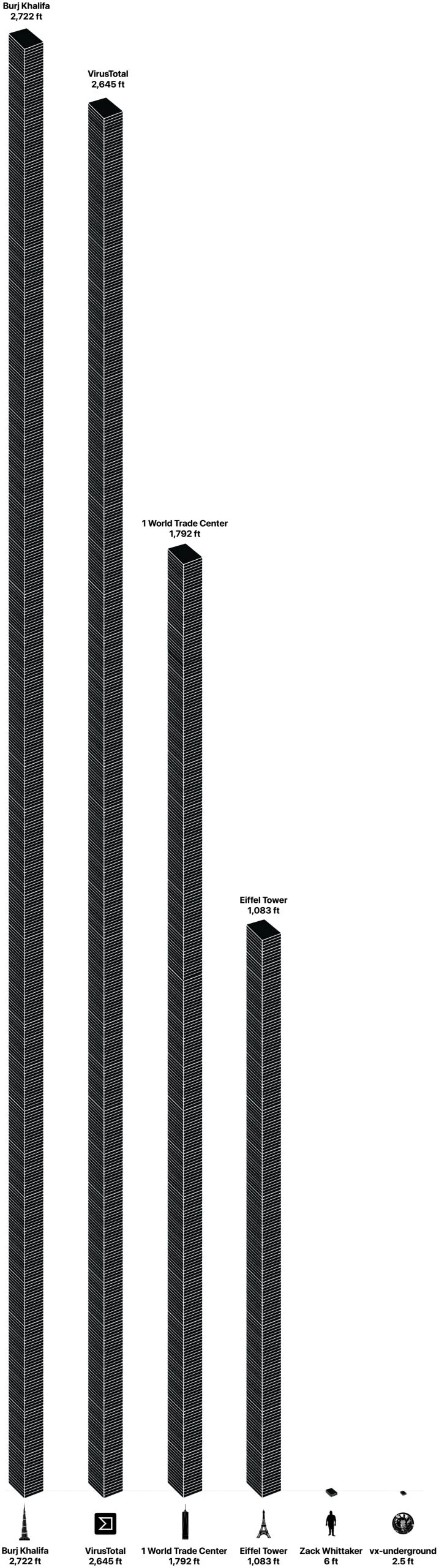
The claim, disseminated by Handala on its public platform, included visual evidence in the form of images depicting a younger Patel, alongside a link purportedly leading to a trove of files originating from what appears to be his personal Gmail account. This digital evidence immediately sparked concern among cybersecurity experts and national security analysts. Independent analysis conducted by TechCrunch indicated that at least some of the electronic messages released by Handala were indeed consistent with communications sent from Patel’s alleged Gmail account. This verification process involved scrutinizing message headers, which contain crucial data used by email delivery systems to authenticate the sender and ensure the legitimacy of a message. These cryptographic signatures provided a strong indication of the authenticity of the checked emails. Furthermore, the investigation uncovered instances where Patel seemingly forwarded communications from his former Justice Department email address to his personal Gmail account as far back as 2014, with those messages also appearing to be genuine. The full cache of leaked files reportedly spans a period up to approximately 2019.
Neither the Federal Bureau of Investigation (FBI) nor the Department of Justice (DOJ) immediately provided a public statement in response to inquiries regarding the alleged breach. However, Reuters, which initially reported on the alleged email leaks, indicated that an official within the Justice Department had acknowledged the incident.
The Target: A High-Profile Official
Kash Patel is a figure well-known in American political and national security circles, having held several influential positions within the U.S. government. His career trajectory includes roles as a prosecutor for the Department of Justice, a staffer on the House Intelligence Committee, a senior director on the National Security Council, and as Chief of Staff to the Acting Secretary of Defense during the Trump administration. His various capacities involved access to highly classified information and participation in critical national security decisions. The targeting of an individual with such a background underscores the strategic intent behind the attack, aiming potentially for intelligence gathering, reputational damage, or a demonstration of cyber capabilities. The fact that the alleged breach involved a personal email account, rather than a government-issued one, highlights a persistent vulnerability for public officials, as the line between professional and private digital lives often blurs.
The Attacker: Handala’s Modus Operandi
The group identifying itself as Handala has emerged as a significant player in the realm of state-sponsored cyber warfare, explicitly aligning itself with Iranian interests. U.S. prosecutors have formally attributed the operations of the Handala group to the Iranian Ministry of Intelligence and Security (MOIS), classifying them as a direct extension of Tehran’s cyber capabilities. This attribution solidifies the understanding that Handala is not merely a "hacktivist" collective but rather a sophisticated, government-backed entity engaged in strategic cyber operations.
Handala’s tactics typically involve a blend of data exfiltration, public shaming, and disruptive attacks. Their campaigns often coincide with periods of heightened geopolitical tension, suggesting a direct correlation between their activities and the broader foreign policy objectives of the Iranian state. The group’s digital footprint is characterized by agility, quickly adapting to countermeasures and re-establishing its online presence even after law enforcement interventions.
Verifying the Digital Footprint
The process of authenticating leaked data, especially in politically charged cyberattacks, is crucial for journalistic integrity and public trust. In this instance, the verification relied on technical details embedded within email message headers. These headers contain metadata, such as sender IP addresses, mail server routes, and cryptographic signatures (like DKIM, DMARC, and SPF), which are difficult to forge convincingly for a large volume of emails. The presence of valid cryptographic signatures strongly suggests that the emails were indeed sent from the claimed account, rather than being fabricated. This meticulous verification helps distinguish genuine breaches from disinformation campaigns, a growing challenge in the current information landscape. The dated nature of the files, extending up to 2019, suggests that the attackers may have had access for some time, or that the current leak is a subset of a larger compromised dataset.
A Broader Landscape of Cyber Warfare
The alleged breach of Patel’s personal email account is not an isolated incident but rather a symptom of an escalating global cyber conflict, particularly between the U.S. and Iran. For years, both nations have engaged in a tit-for-tat exchange of cyberattacks, targeting critical infrastructure, government agencies, and individuals deemed strategically important. Iran, in particular, has developed a formidable cyber capability, evolving from relatively unsophisticated attacks to highly targeted and persistent operations. These efforts are often driven by a combination of factors, including intelligence gathering, retaliation against perceived aggressions, and a desire to project power and sow discord among adversaries.
The blurring lines between traditional espionage and cyber warfare mean that personal accounts of public figures, even those no longer in active government roles, remain attractive targets. Such accounts can contain a wealth of information, from personal contacts and financial details to insights into past official communications or even current activities, making them valuable assets for foreign intelligence services.
Escalating Tensions and Recent Campaigns
The alleged attack against Patel occurs amidst a backdrop of significantly heightened geopolitical tensions, particularly those involving the U.S., Israel, and Iran. Handala has notably intensified its cyber campaigns in recent months. For example, the group claimed responsibility for a highly destructive attack against Stryker, a major medical technology corporation. This incident reportedly resulted in the wiping of tens of thousands of employee devices, causing substantial operational disruption. In response to this and other activities, the FBI took action, seizing several of Handala’s websites. However, demonstrating their resilience and adaptability, the group quickly re-established its online presence on new domains. Beyond corporate targets, Handala has also engaged in publishing the personal details of individuals allegedly affiliated with the Israeli Defense Forces and local defense contractors, signaling a broader strategy aimed at undermining morale and operational security among adversaries. This pattern of activity demonstrates a clear intent to disrupt, expose, and retaliate through cyber means.
Implications for National Security and Personal Privacy
The compromise of a senior official’s personal email carries multifaceted implications. From a national security perspective, even seemingly innocuous personal communications can offer insights into an individual’s network, routines, or vulnerabilities, which could be exploited for more sophisticated attacks. There is also the potential for the leaked information to be used for blackmail, influence operations, or to sow disinformation. For individuals, such breaches are deeply invasive, exposing private lives to public scrutiny and potential misuse.
This incident serves as a stark reminder of the persistent challenge posed by state-sponsored cyber adversaries. Protecting government networks is a monumental task, but securing the personal digital footprint of high-value targets, who may use consumer-grade services for convenience, presents an entirely different layer of complexity. Experts frequently advise public officials and those with access to sensitive information to maintain rigorous cybersecurity practices for all their digital accounts, including strong, unique passwords, multi-factor authentication, and a clear separation between professional and personal communications.
The Blurring Lines of State-Sponsored Activity
The Handala group’s actions exemplify the evolving nature of state-sponsored cyber operations. While traditional intelligence agencies conduct clandestine espionage, groups like Handala often operate in a semi-public sphere, using social media and dedicated websites to announce their exploits. This public posturing serves multiple purposes: it takes credit for operations, demonstrates capability to adversaries, intimidates targets, and rallies support among sympathizers. The distinction between "hacktivism" and direct state-sponsored cyber warfare becomes increasingly blurred, making attribution and response more challenging.
Neutral analytical commentary often highlights that such groups provide a degree of plausible deniability for states, allowing them to exert cyber influence without direct, overt government involvement. However, the formal accusation by U.S. prosecutors linking Handala directly to the Iranian MOIS strips away much of that plausible deniability, underscoring the direct governmental hand in these operations.
Looking Ahead: Challenges in Cyber Defense
The alleged breach of Kash Patel’s personal email account reinforces the urgent need for enhanced cybersecurity measures across all sectors, particularly for individuals in sensitive positions. It underscores the critical importance of continuous vigilance, robust threat intelligence sharing, and public awareness campaigns about the risks of phishing, social engineering, and poor password hygiene. As geopolitical tensions continue to manifest in the digital domain, the battle for information superiority and defensive resilience will only intensify. The incident serves as a stark reminder that the personal digital security of key figures is inextricably linked to national security, demanding a holistic approach to protection that extends beyond official government networks. The ability of groups like Handala to rapidly adapt and reconstitute themselves further complicates defensive efforts, requiring a dynamic and proactive strategy from targeted nations and organizations.