In the complex and often abstract world of cybersecurity, the sheer scale of digital threats can be challenging to grasp. Yet, two prominent entities within the cybersecurity research community have recently offered a tangible perspective on the monumental volume of malicious code and samples they meticulously collect and analyze. These vast digital repositories, essential for understanding and combating cybercrime, translate into an astonishing physical presence when imagined as stacks of conventional hard drives, painting a vivid picture of the relentless battle against evolving digital adversaries.
The Digital Battlefield: A Growing Threat Landscape
The journey of digital threats began subtly in the early days of computing, with rudimentary viruses like the "Elk Cloner" for Apple II systems in 1982, spreading via floppy disks. These early forms were often pranks or demonstrations of technical prowess. However, the advent of the internet in the 1990s and the subsequent explosion of networked computing transformed malware from isolated curiosities into a pervasive, global menace. Viruses evolved into worms that self-propagated across networks, trojans disguised as legitimate software, and sophisticated spyware designed for espionage.
By the 21st century, the landscape had become significantly more hostile. The proliferation of broadband internet, always-on connections, and the increasing reliance on digital infrastructure for everything from personal communication to critical national services created fertile ground for cybercriminals. Malware became a tool for financial gain, political disruption, and state-sponsored espionage. Ransomware, which encrypts a victim’s data and demands payment for its release, emerged as a particularly lucrative and disruptive threat, exemplified by attacks like WannaCry and NotPetya, which crippled organizations worldwide in 2017. These events underscored the devastating real-world impact of digital threats, costing billions in damages, disrupting healthcare systems, and bringing supply chains to a halt.
This relentless evolution of cyber threats necessitates an equally sophisticated and continuous defense. Cybersecurity firms, intelligence agencies, and independent researchers are locked in a perpetual arms race with threat actors. A crucial component of this defense is the collection and analysis of malware samples and their underlying source code. By dissecting these digital pathogens, defenders can identify patterns, understand attack methodologies, develop countermeasures, and predict future threats. Without such comprehensive archives, the task of safeguarding the digital realm would be akin to fighting an invisible enemy with no intelligence.
Guardians of the Gates: The Role of Malware Repositories
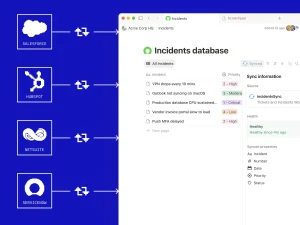
Among the pivotal players in this defensive effort are organizations like vx-underground and VirusTotal. vx-underground, a research group dedicated to the study of malware, has amassed what it claims is the world’s largest collection of malware source code. This archive, publicly stated to be approximately 30 terabytes (TB) of data, represents a treasure trove for reverse engineers and security analysts seeking to understand the fundamental building blocks of cyberattacks. Access to source code allows for deep dives into malware functionality, vulnerability exploitation, and the development of more robust detection mechanisms.
In parallel, VirusTotal, an online service founded by Bernardo Quintero and later acquired by Google, offers a complementary but vastly larger repository. It aggregates data from numerous antivirus engines and security tools to scan files and URLs for malicious content. Users contribute samples, creating an immense, crowd-sourced database of active threats. Quintero recently highlighted the astonishing scale of VirusTotal’s collection, stating it holds approximately 31 petabytes (PB) of malware samples contributed by its global user base. To put this into perspective, one petabyte is roughly equivalent to 1,000 terabytes. This difference in scale reflects the distinct nature of their collections: vx-underground focuses on the intricate source code, while VirusTotal deals with the sheer volume of executable malicious files encountered in the wild.
These repositories are not merely static libraries; they are dynamic, constantly updated databases that serve as critical infrastructure for the entire cybersecurity ecosystem. Threat intelligence firms leverage these datasets to identify emerging campaigns and attacker tactics. Artificial intelligence and machine learning researchers use them to train advanced detection models that can spot novel or polymorphic malware variants that evade traditional signature-based defenses. Without the ability to study vast quantities of both benign and malicious code, AI systems would lack the necessary data to learn the subtle indicators of compromise. Furthermore, these archives facilitate forensic investigations, allowing security professionals to compare suspicious files against known threats and trace the lineage of malware families. The collaborative nature of VirusTotal, in particular, demonstrates the power of collective intelligence in cybersecurity, where individual contributions collectively build a formidable defense asset.
Quantifying the Invisible: A Physical Analogy
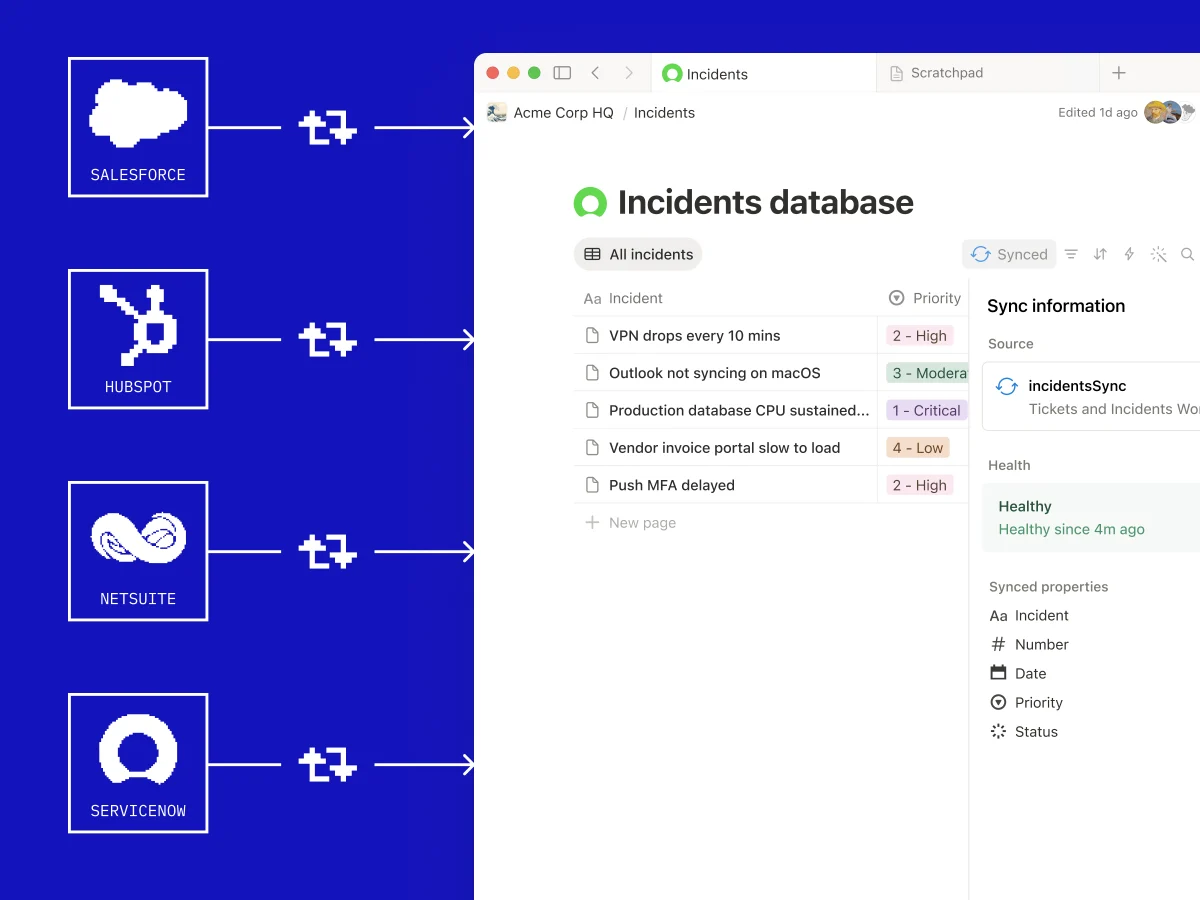
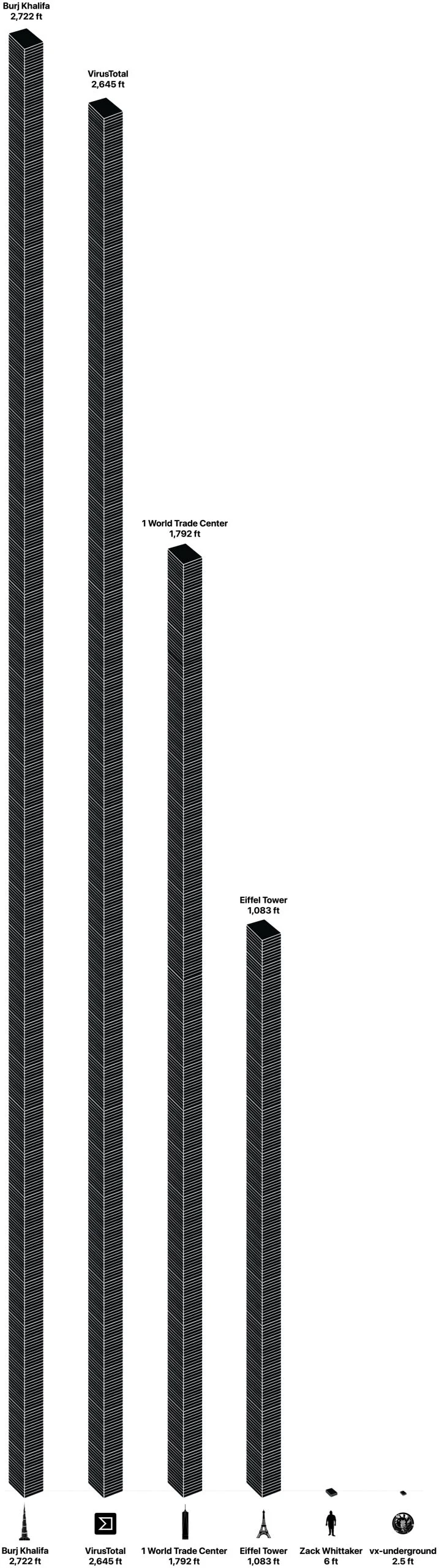
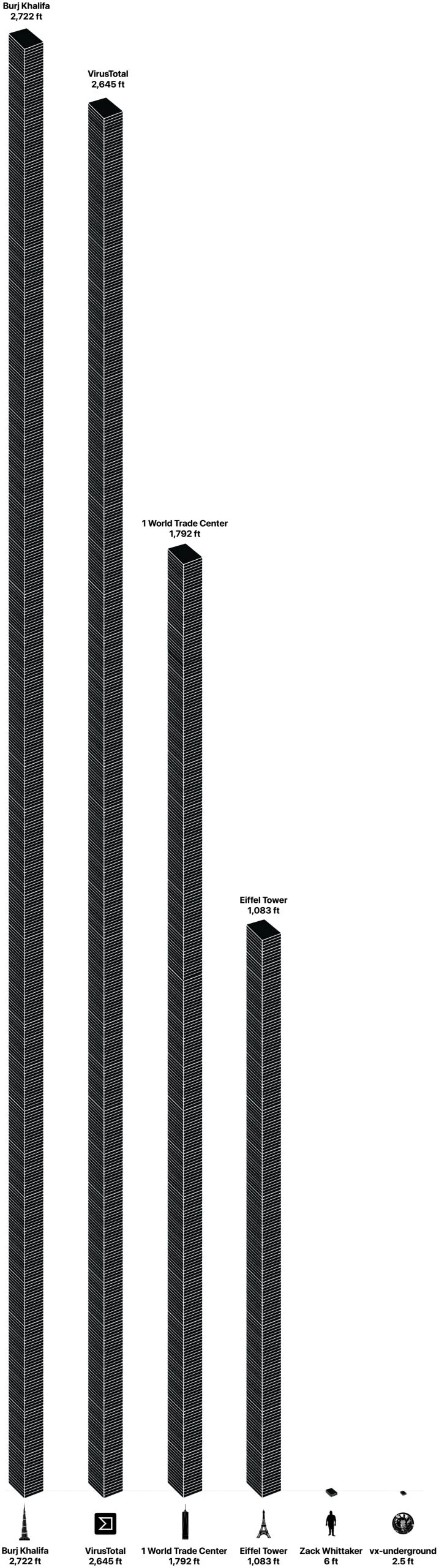
To comprehend the true scale of these digital fortresses, it becomes necessary to translate their ethereal data into a more relatable physical form. Imagine these terabytes and petabytes of information stored on conventional 3.5-inch internal hard drives, each with a capacity of 1 terabyte and a standardized height of approximately one inch. This thought experiment offers a compelling visual analogy for the invisible war being waged online.
For vx-underground’s reported 30 terabytes of malware source code, the physical manifestation would be relatively modest, yet significant. Stacking 30 one-terabyte hard drives on top of one another would result in a column approximately 30 inches tall, or about 2.5 feet. This height is comparable to a small filing cabinet or a stack of common household items, a manageable representation for a highly specialized archive.
However, the scale dramatically shifts when considering VirusTotal’s 31 petabytes of user-contributed malware samples. Converting 31 petabytes into terabytes yields 31,744 terabytes (since 1 PB = 1024 TB, though commonly approximated as 1000 TB for simpler visualization). If each terabyte were stored on a single 1-inch-high hard drive, stacking these drives would create an imposing structure of 31,744 inches. This translates to an astonishing 2,645 feet.
To provide even greater context, this towering stack of hard drives would nearly rival some of the world’s most iconic superstructures. The Burj Khalifa in Dubai, currently the world’s tallest building, stands at a breathtaking 2,722 feet. VirusTotal’s data, if physically stacked, would fall just shy of this architectural marvel. In another comparison, the Eiffel Tower in Paris measures 1,083 feet from its base to the tip of its flagpole. This means VirusTotal’s malware archive would be approximately two and a half times the height of the Eiffel Tower, underscoring the immense volume of malicious digital artifacts circulating and being collected globally.
This visualization highlights the exponential growth of data in the digital age and, more specifically, the relentless proliferation of cyber threats. It moves the abstract concept of "big data" into a concrete, awe-inspiring perspective, making the digital struggle more tangible.
The Unseen War: Implications of Data Scale
The sheer volume of malware data collected by these organizations carries profound implications for the ongoing battle for digital security. Firstly, it underscores the persistent and escalating nature of cybercrime. The fact that threat actors are continuously developing and deploying such an immense quantity of malicious code means that the defensive effort can never truly rest. New variants emerge daily, requiring constant vigilance and updates to security systems.
Secondly, this data deluge presents significant challenges for storage, processing, and analysis. Managing petabytes of data requires massive computational resources, advanced data centers, and sophisticated analytics platforms. The costs associated with maintaining such infrastructure are substantial, highlighting the economic investment required to safeguard digital environments. Furthermore, extracting meaningful insights from such vast, unstructured datasets demands cutting-edge techniques, including advanced machine learning and artificial intelligence, to identify patterns, classify threats, and predict future attack vectors automatically. Manual analysis of even a fraction of this data would be an impossible task.
Thirdly, the existence of such comprehensive repositories is a double-edged sword. While invaluable for defense, the aggregation of malware source code or samples could, in theory, become a target for highly motivated threat actors seeking to reverse-engineer defenses or even create new, more potent variants by studying existing ones. However, the benefits for legitimate cybersecurity research and defense far outweigh these theoretical risks, as these organizations typically employ robust security measures to protect their sensitive collections.
Finally, the analogy of physical height helps to convey the "tip of the iceberg" phenomenon in cybersecurity. While these archives are massive, they primarily represent known malware and observed threats. The constant emergence of zero-day vulnerabilities and entirely novel attack techniques means that the true, full scope of malicious activity is likely even larger and more dynamic than what is currently cataloged. This reinforces the need for proactive security measures, threat hunting, and continuous innovation rather than solely relying on reactive defenses based on known signatures.
Looking Ahead: The Future of Cybersecurity Defense
As our world becomes increasingly interconnected and reliant on digital systems, the volume and sophistication of cyber threats are expected to continue their upward trajectory. The monumental archives maintained by organizations like vx-underground and VirusTotal will only grow, reflecting the ongoing digital arms race. The future of cybersecurity defense will undoubtedly lean heavily on advanced technologies capable of processing and understanding this data at an unprecedented scale.
Artificial intelligence and machine learning will play an increasingly critical role, not just in detecting known threats but in identifying anomalous behavior that could indicate novel attacks. Automation will become essential for rapid response and mitigation. Furthermore, the collaborative efforts exemplified by VirusTotal’s community contributions will remain vital, fostering a collective defense posture against a globally distributed adversary.
Ultimately, the ability to visualize the sheer physical scale of these malware archives serves as a stark reminder of the persistent and evolving threat landscape. It underscores the immense effort and resources dedicated by cybersecurity professionals worldwide to protect our digital lives, ensuring that the invisible empire of malware does not become an insurmountable force. The silent, tireless work of collecting, analyzing, and understanding these digital threats is the unseen foundation upon which our modern, interconnected world securely operates.