For years, the conventional wisdom among cybersecurity professionals held that penetrating Apple’s iOS ecosystem presented a formidable challenge. The prevailing belief was that uncovering vulnerabilities and developing functional exploits for iPhones demanded extraordinary time, immense financial resources, and the specialized expertise of dedicated research teams to bypass its multi-layered security architecture. This perception fostered an assumption that sophisticated spyware and "zero-day" vulnerabilities—flaws unknown to the software vendor before their active exploitation—were exceedingly rare and exclusively deployed in highly restricted, precision-targeted operations, a claim echoed by Apple itself.
However, recent developments have starkly contradicted this long-held assumption, signaling a significant shift in the mobile security landscape. Over the past month, leading cybersecurity firms including Google, iVerify, and Lookout have meticulously documented several widespread hacking campaigns. These operations leverage potent tools, identified as "Coruna" and "DarkSword," to indiscriminately target a vast global user base still operating on older versions of Apple’s mobile software. The disconcerting revelation is that some of these advanced tools have now found their way into the public domain, effectively democratizing the ability to launch attacks against millions of iPhones that lack the most current security patches.
The Evolution of iPhone Security and its Reputation
Apple has assiduously cultivated a reputation for prioritizing user privacy and device security, often positioning its products as a safer alternative in a digitally perilous world. From the introduction of the Secure Enclave processor, which isolates sensitive data like biometrics, to the implementation of sandboxing techniques that restrict app access to system resources, Apple has consistently invested in fortifying its operating systems and hardware. The company’s commitment to security has historically been a cornerstone of its brand identity, fostering a high degree of user trust. This focus intensified in the mid-2010s and early 2020s, as incidents involving state-sponsored hacking and the proliferation of commercial spyware like Pegasus began to highlight the critical need for robust mobile defenses.
In response to an escalating threat landscape, Apple has continued to pour substantial resources into advanced security research and development. The latest iterations of its hardware and software exemplify this commitment. For instance, the release of the iPhone 17 models in 2025, coupled with iOS 26, introduced groundbreaking technologies like memory-safe code. This fundamental shift in programming aims to prevent entire classes of vulnerabilities that traditionally underpin many sophisticated attacks. Furthermore, features such as Lockdown Mode, specifically designed to offer extreme, albeit restrictive, protection against potential spyware incursions, underscore Apple’s proactive stance. The overarching objective of these innovations has been to further harden modern iPhones against exploitation, reinforcing the company’s assertion that its devices are exceptionally difficult to compromise.
Emergence of Widespread Threats: Coruna and DarkSword
The emergence of Coruna and DarkSword, however, presents a formidable challenge to this narrative. These sophisticated exploit chains demonstrate a capacity for broader targeting than previously understood. Investigations by cybersecurity researchers indicate that the perpetrators behind these campaigns include actors linked to nation-states, such as Russian intelligence services, and organized Chinese cybercriminal groups. Their modus operandi typically involves luring victims to compromised websites or deceptive landing pages, which then silently deploy the exploits to gain unauthorized access to the device. Once compromised, these tools can exfiltrate sensitive data, including personal communications, location information, and financial details, on a massive scale.
DarkSword, in particular, has been identified as heavily reliant on memory corruption bugs—a prevalent category of software flaws where a program incorrectly manages memory, leading to system instability or, critically, allowing an attacker to execute malicious code. Google’s analysis of DarkSword revealed its intricate design, capable of chaining multiple vulnerabilities to achieve persistent device compromise. The discovery of such tools being actively used in widespread campaigns, rather than isolated incidents, suggests a significant evolution in the tactics and reach of mobile adversaries. The subsequent leak of components of these exploit kits onto the open internet marks a perilous turning point, effectively lowering the barrier to entry for a broader spectrum of malicious actors, from opportunistic cybercriminals to less technically proficient individuals seeking to exploit these newly available capabilities.
The Perilous Divide: Old vs. New iOS
This escalating threat landscape has, in effect, created a two-tiered security structure among iPhone users, bifurcating the user base into distinct classes of vulnerability. On one side are users who diligently update their devices, running the most recent iOS 26 on contemporary iPhone 17 models or newer. These users benefit from Apple’s cutting-edge defenses, including the "Memory Integrity Enforcement" feature. This critical security enhancement is specifically engineered to thwart memory corruption bugs, which, as evidenced by DarkSword, are frequently exploited in spyware and device-unlocking attacks. By making these foundational vulnerabilities significantly harder to exploit, Apple aims to protect its most current users from the most prevalent forms of mobile intrusion.
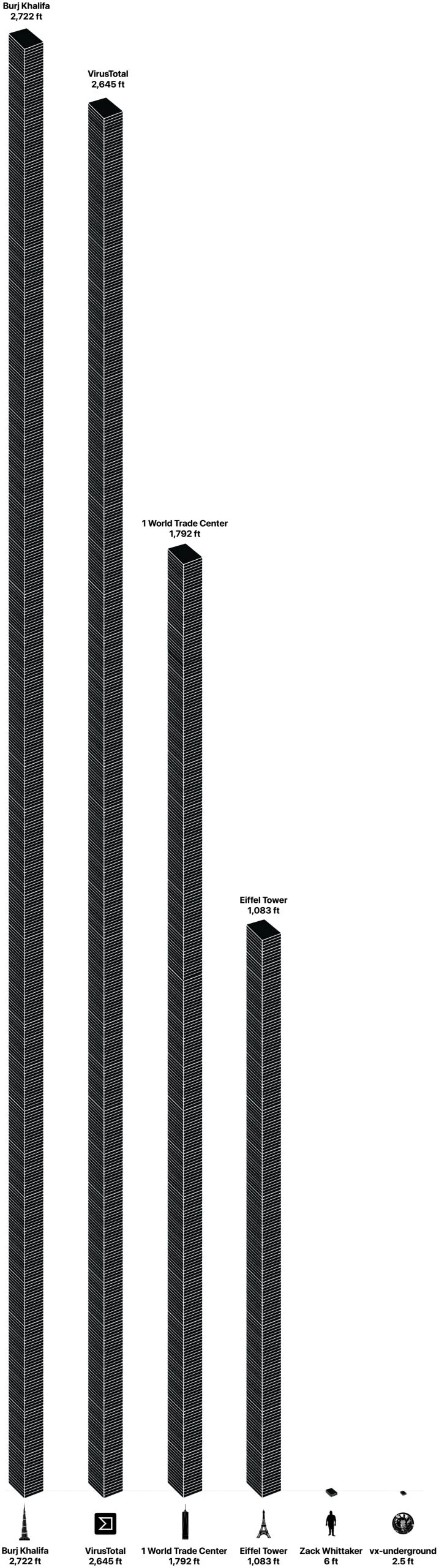
Conversely, a substantial segment of iPhone users remains on older operating system versions, such as iOS 18 or even earlier iterations. These legacy devices, while still functional, lack the advanced security mitigations integrated into the latest software and hardware. Consequently, they remain susceptible to the very memory-based hacks and other exploits that have been addressed in newer releases. This digital divide is not merely theoretical; it translates into tangible risk. The discovery and subsequent proliferation of tools like Coruna and DarkSword directly imply that older, less "memory-safe" iPhones and iPads are increasingly easy targets for a growing cohort of spyware-wielding state actors and cybercriminals. The sheer volume of these older, unpatched devices represents a vast, vulnerable attack surface that sophisticated and opportunistic attackers are now actively exploiting.
The Lucrative Exploit Market and its Ramifications
The commercial cybersecurity sector has keenly observed these developments, with experts from companies like iVerify and Lookout—firms with a vested interest in mobile security solutions—emphasizing the gravity of the situation. Their analysis suggests that the prevalence of tools like Coruna and DarkSword fundamentally challenges the long-held assumption that iPhone hacks are inherently rare. Matthias Frielingsdorf, co-founder of iVerify, candidly stated that mobile attacks are now "widespread." While acknowledging that zero-day exploits targeting the absolute latest software versions will always command a premium and thus likely remain reserved for highly specific targets, the current trend indicates a broader commodification of exploits for slightly older, yet still widely used, systems.
Patrick Wardle, a prominent Apple security expert, offers a critical perspective on the language often used to describe these attacks. He argues that labeling iPhone compromises as "rare" or "highly advanced" can be misleading, primarily because their documentation is infrequent, not necessarily because the attacks themselves are uncommon. Wardle posits that such sophisticated capabilities are increasingly becoming a baseline for national-level actors, accessible to many nations or procurable for the right price, rather than representing an exceptional tier of technical prowess.
Adding another layer of complexity is the burgeoning "second-hand" market for exploits. Justin Albrecht, a principal researcher at Lookout, highlights how this market creates a perverse financial incentive. Exploit developers and individual brokers can, in essence, profit twice from the same vulnerability. Once an initial exploit is discovered and potentially patched by the vendor, its utility doesn’t vanish entirely. Instead, it can be repurposed and resold for use against the vast installed base of devices that haven’t yet updated, or cannot update, to the patched version. This secondary market ensures a prolonged lifespan for vulnerabilities, maximizing their financial yield and fueling a continuous cycle of exploitation. Albrecht warns that this phenomenon is not an isolated incident but rather "a sign of things to come," indicating a systemic shift in the economics of cyber warfare and cybercrime.
Broader Implications for Digital Security
The implications of this evolving threat landscape extend far beyond individual device security. At a societal level, the erosion of trust in widely used mobile platforms could have profound effects. Users rely on their smartphones for virtually every aspect of their digital lives, from sensitive communications to financial transactions. A widespread perception of vulnerability could undermine this trust, leading to increased anxiety and potentially altering user behavior. Culturally, it underscores the growing digital divide, where access to the latest, most secure technology becomes a de facto prerequisite for robust personal security, leaving those with older devices disproportionately exposed.
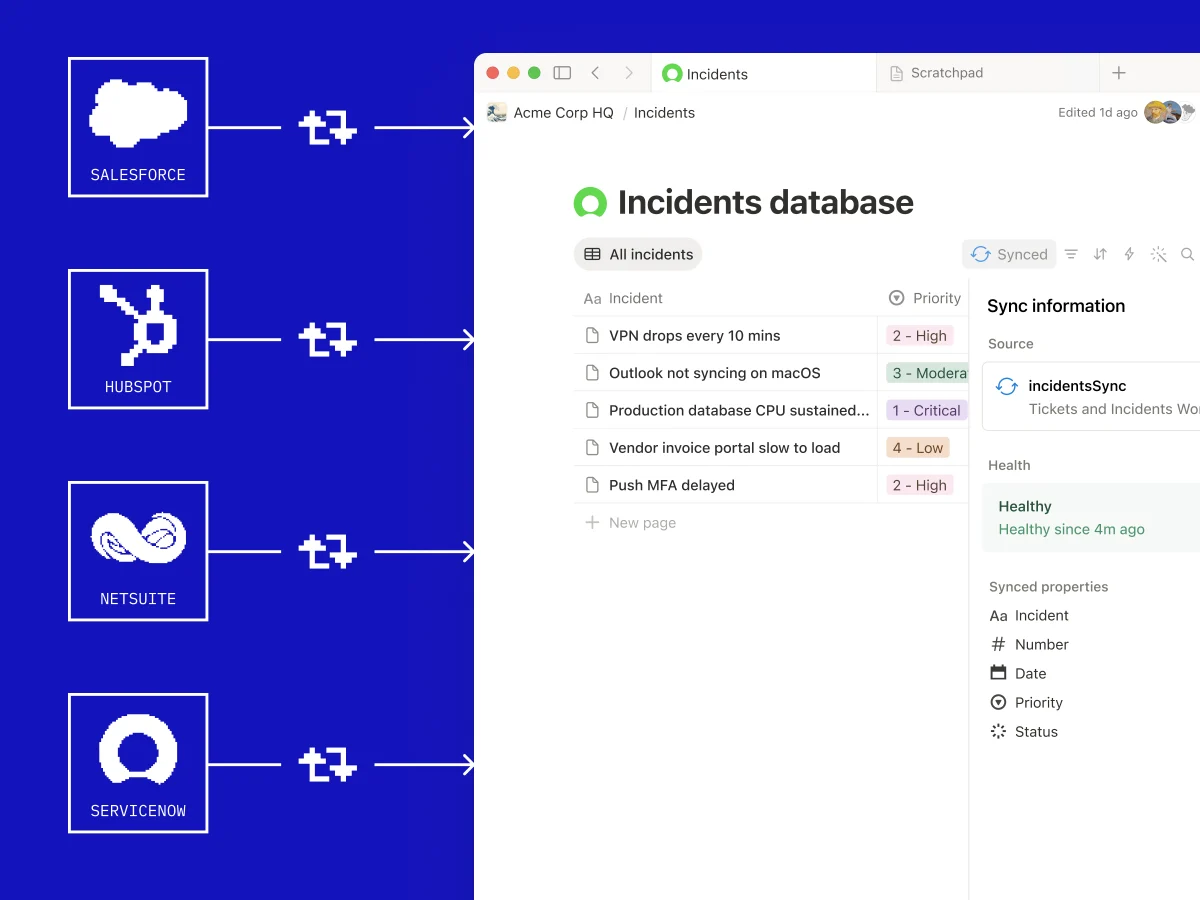
For enterprises, the increased risk poses significant challenges, particularly in environments supporting Bring Your Own Device (BYOD) policies. Organizations must now contend with a heterogeneous device landscape where the security posture of an employee’s personal phone can directly impact corporate data and networks. The geopolitical dimension is also undeniable, with nation-state involvement in developing and deploying these tools raising questions about digital sovereignty, international cyber norms, and the weaponization of vulnerabilities for espionage and influence.
Navigating the Future of Mobile Defense
The current situation necessitates a multi-faceted response from both technology providers and users. Apple, despite its significant investments, faces the ongoing challenge of securing an immense and diverse installed base while balancing innovation with backward compatibility. Encouraging users to update their devices promptly, providing clear and accessible information about security risks, and potentially extending security support for older hardware for longer periods could be crucial steps.
For individual users, the message is unequivocal: regular software updates are not merely about accessing new features; they are fundamental to digital hygiene and personal security. Understanding the risks associated with older operating systems and making informed decisions about device upgrades are increasingly important. Furthermore, exercising caution when clicking on suspicious links or visiting unfamiliar websites, particularly on older devices, becomes paramount.
The shift from highly targeted, bespoke attacks to more widespread exploitation of legacy systems signals a critical juncture in mobile cybersecurity. The leakage of advanced hacking tools into the public domain has democratized capabilities once reserved for elite actors, profoundly altering the threat landscape. As the digital world becomes ever more intertwined with personal and professional life, confronting this widening security divide and adapting to the new realities of pervasive mobile threats will be essential for safeguarding digital futures.