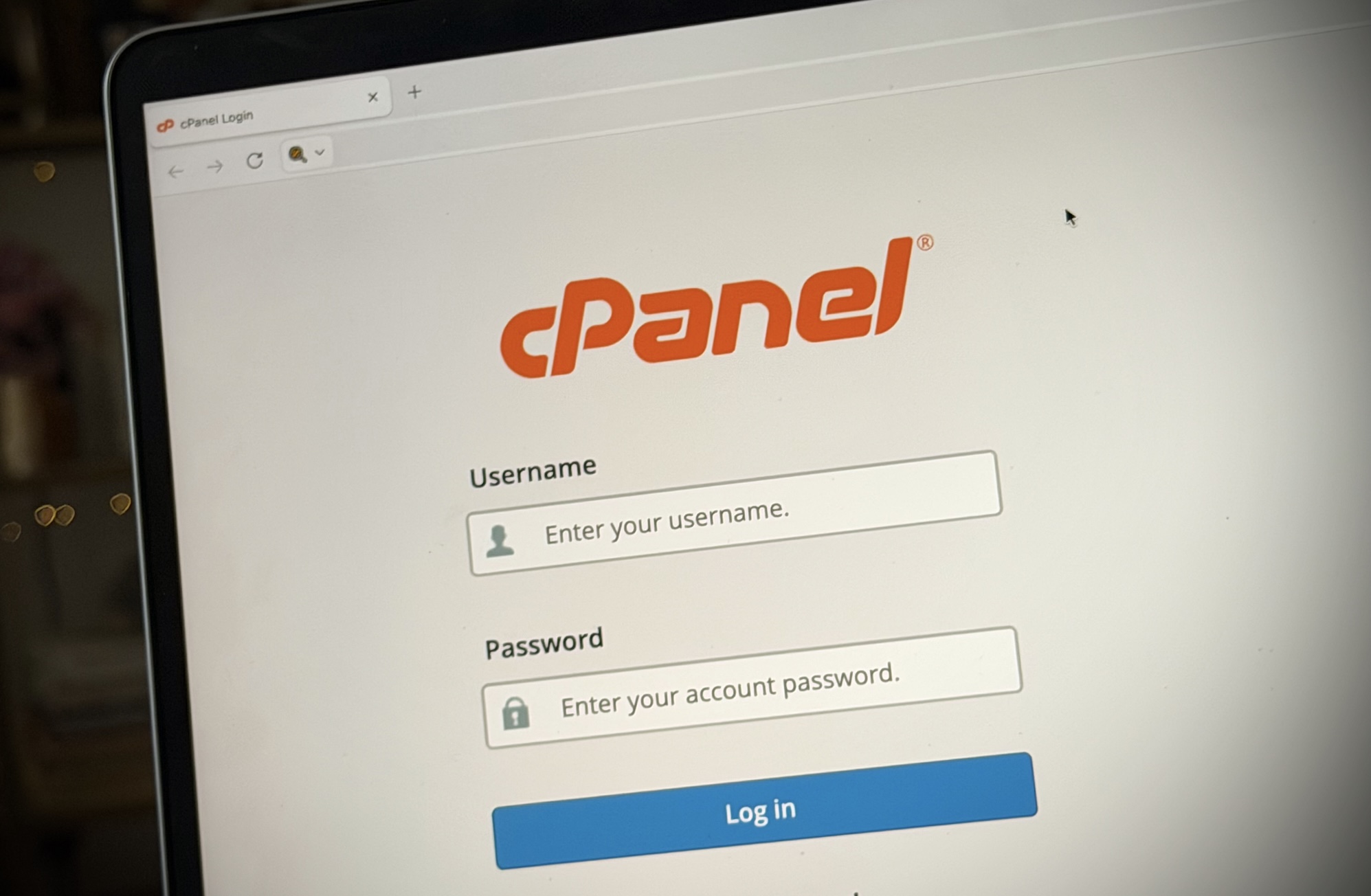
Security experts globally are issuing a severe alert regarding a newly identified and actively exploited flaw within cPanel and WebHost Manager (WHM), pervasive software solutions central to managing millions of websites worldwide. This critical vulnerability permits malicious actors to bypass authentication protocols, gain unauthorized access, and ultimately seize complete control over affected web servers, posing a substantial threat to digital infrastructure. The extensive adoption of cPanel and WHM across the web hosting sector amplifies the potential reach of this exploit, necessitating immediate and comprehensive patching efforts from hosting providers and site administrators alike.
Understanding cPanel’s Critical Role
cPanel, often paired with WHM, stands as a cornerstone of the modern web hosting ecosystem. For decades, it has provided an intuitive, graphical user interface (GUI) that simplifies the complex task of managing web servers. Before its advent, administering a web server typically required deep command-line knowledge, a significant barrier for many individuals and small to medium-sized businesses (SMBs) seeking an online presence. cPanel democratized web hosting by offering an accessible control panel for tasks such as creating websites, managing email accounts, configuring databases, uploading files, and handling domain settings.
Its widespread use stems from its ease of deployment and user-friendliness, making it the preferred choice for countless commercial web hosting companies. These providers often bundle cPanel with their shared hosting packages, allowing customers without extensive technical expertise to manage their digital assets effectively. From a single dashboard, users can control virtually every aspect of their online operations, from e-commerce sites to personal blogs and corporate portals. This deep integration and administrative power, while a significant convenience, also mean that a vulnerability within cPanel itself grants attackers a potent key to the entire server environment it manages. The software effectively serves as the "master key" to the digital properties residing on a server, underscoring the gravity of any security compromise.
The Nature of the Vulnerability: CVE-2026-41940
The vulnerability, officially cataloged as CVE-2026-41940, represents a severe authentication bypass flaw. This particular exploit allows an unauthorized individual to circumvent the standard login procedures for cPanel’s administrative panel, thereby gaining unrestricted access to the server. The implications are profound: once inside, a cybercriminal can perform a wide array of malicious actions, including but not limited to, injecting malware into websites, stealing sensitive user data, defacing web pages, redirecting traffic to malicious sites, or even using the compromised server as a launchpad for further attacks.
Historically, authentication bypass flaws are among the most dangerous categories of vulnerabilities. Unlike exploits that require intricate system knowledge or specific user interactions, an authentication bypass offers a direct route to administrative privileges. This simplicity of exploitation, combined with the ubiquitous nature of cPanel, creates a "perfect storm" for potential widespread digital disruption. The threat isn’t merely theoretical; evidence suggests active exploitation has been underway, turning a potential risk into an immediate crisis for unpatched systems.
A Race Against Exploitation: Industry Response
The revelation of CVE-2026-41940 has triggered a rapid and coordinated response across the web hosting industry. Recognizing the immense danger posed by the flaw, cPanel’s developers have released patches for all supported versions of their software. The onus is now on hosting providers and individual server administrators to implement these updates without delay. Many prominent commercial web hosting companies, understanding their critical role in maintaining internet security, have moved swiftly to patch their customer systems.
Major players like Namecheap and HostGator have publicly acknowledged the vulnerability and detailed their response strategies. Namecheap, for instance, took the proactive step of temporarily blocking customer access to cPanel panels upon learning of the flaw. This drastic measure was implemented to prevent any further exploitation while their technical teams worked diligently to apply the necessary patches across their vast infrastructure. HostGator similarly confirmed the patching of its systems, characterizing the bug as a "critical authentication-bypass exploit," a designation that underscores the severity of the threat. These immediate and decisive actions by large hosting providers highlight the industry’s commitment to safeguarding user data and maintaining service integrity, yet the challenge remains for smaller providers and individual administrators who may not have the same resources or immediate awareness.
Evidence of Pre-Disclosure Attacks
Perhaps the most alarming aspect of this vulnerability is the discovery that malicious actors were already attempting to exploit it months before its public disclosure and the release of official patches. Daniel Pearson, CEO of KnownHost, a web hosting company, revealed in a public forum that his firm observed exploitation attempts as early as February 23, preceding the official disclosure date by a significant margin. This indicates that the vulnerability was a "zero-day" exploit for a period, meaning attackers were aware of and leveraging the flaw before the vendor had developed or distributed a fix.
KnownHost’s telemetry showed signs of unauthorized attempted access on approximately 30 servers within their network, out of thousands. While Pearson noted that these were primarily "attempts" and did not show clear signs of active compromise, the presence of such activity underscores the sophisticated nature of cyber adversaries and the constant race between attackers and defenders. This pre-disclosure exploitation complicates the remediation process, as it means some systems may have already been compromised before administrators even knew a patch was available. It also reinforces the notion that even with rapid response, the window for attack can be significant, emphasizing the importance of robust security monitoring and incident response capabilities. The revelation further indicates a potential supply chain risk, as cPanel also rolled out a security fix for WP Squared, a tool often used for managing WordPress websites, suggesting a broader impact across related software ecosystems.
Broader Implications for Web Security
The cPanel vulnerability serves as a stark reminder of the interconnectedness and inherent fragilities within the global digital infrastructure. The ripple effects of such a widespread flaw extend far beyond individual websites, touching upon several critical aspects of internet security and digital trust.
Economic and Reputational Impact: For businesses, a compromised website can lead to significant financial losses. This includes direct costs for remediation, potential legal liabilities due to data breaches, and severe damage to brand reputation and customer trust. Small businesses, often relying heavily on their online presence, are particularly vulnerable, as they may lack the resources to recover quickly from a major cyber incident.
Supply Chain Security: cPanel is a foundational component for countless web hosts, making it a critical link in the software supply chain. A vulnerability in such a widely used tool demonstrates how a single point of failure can impact an entire ecosystem. This highlights the growing importance of supply chain security, where the security posture of third-party software and services becomes paramount. Organizations must increasingly scrutinize the security practices of their vendors, understanding that a weakness anywhere in the chain can affect them directly.
User Trust and Data Privacy: At the end of the chain are the users who interact with these websites. A server takeover could expose sensitive personal information, including login credentials, financial data, and private communications. Such breaches erode public trust in online services and raise significant privacy concerns, potentially leading to identity theft and other forms of cybercrime. The repeated occurrence of such incidents can foster a climate of distrust, discouraging online engagement.
Cybersecurity Preparedness: This incident underscores the ongoing challenge of maintaining cybersecurity in a dynamic threat landscape. It emphasizes the necessity for continuous vigilance, proactive patching, and robust incident response plans. For hosting providers, this means investing in advanced threat detection systems, automated patching mechanisms, and dedicated security teams. For end-users, it means choosing reputable hosting providers, regularly updating their own website software (like WordPress or Joomla), and implementing strong security practices such such as multi-factor authentication.
Path Forward: Securing the Digital Frontier
The immediate priority for all entities utilizing cPanel or WHM is to verify that the necessary security patches for CVE-2026-41940 have been successfully applied. For customers of managed hosting services, confirming with their provider about the status of these patches is crucial. Self-managed server administrators must take direct action to update their systems promptly. Beyond immediate patching, this incident offers broader lessons for enhancing digital security posture.
Moving forward, the cybersecurity community and industry must continue to collaborate on identifying and mitigating vulnerabilities more swiftly. This includes fostering responsible disclosure programs, where researchers can report flaws without fear of retribution, allowing vendors to develop fixes before widespread exploitation occurs. Furthermore, investing in automated security tools and continuous monitoring can help detect and respond to suspicious activity, even before official patches are released for zero-day exploits. The incident also reinforces the need for diversification of control panels and server management solutions where feasible, to reduce the impact of a single point of failure. Ultimately, ensuring a secure digital environment requires a collective commitment to vigilance, rapid response, and a proactive approach to cybersecurity at every level of the internet infrastructure.