The digital landscape witnessed a significant disruption as the public-facing infrastructure of Ubuntu, a widely adopted Linux operating system, and its developer, Canonical, fell victim to a sustained distributed denial-of-service (DDoS) attack. This extensive cyber assault, which commenced on a recent Thursday, severely impacted critical services relied upon by millions of Ubuntu users worldwide, highlighting the vulnerability of even foundational open-source platforms to malicious cyber activities.
Canonical, the British software company responsible for the development and commercial support of Ubuntu, promptly acknowledged the incident. In an official statement disseminated across its communication channels, the company confirmed that its web infrastructure was "under a sustained, cross-border attack" and assured users that it was actively working to address the situation, promising further updates as they became available. The incident underscores the pervasive threat of cyberattacks in an increasingly interconnected digital world, where the stability of core operating systems is paramount for both individual users and vast enterprise networks.
Ubuntu: A Pillar of the Open-Source Ecosystem
To fully grasp the magnitude of this cyberattack, it’s essential to understand Ubuntu’s profound role in the global technology ecosystem. Launched in October 2004, Ubuntu quickly distinguished itself as a user-friendly and robust Linux distribution. Its name, derived from the Nguni philosophy meaning "humanity to others," reflects its core ethos of community and collaboration. Developed and maintained by Canonical, Ubuntu is entirely free and open-source software, making its code publicly available for anyone to use, modify, and distribute.
This accessibility has propelled Ubuntu to become one of the most popular Linux distributions, powering a diverse range of computing environments. From personal desktops and laptops, offering a privacy-focused alternative to proprietary operating systems, to critical server infrastructure underpinning vast swathes of the internet, Ubuntu’s footprint is immense. It’s a prevalent choice for cloud computing platforms, web servers, data centers, and even embedded systems and IoT devices. Developers, researchers, and tech enthusiasts worldwide rely on Ubuntu for its stability, security, and extensive software repositories. An attack on Ubuntu’s infrastructure, therefore, extends far beyond a mere website outage; it directly impacts the ability of countless individuals and organizations to perform essential digital tasks, download updates, and access vital security patches.
The Anatomy of a DDoS Attack
The method employed in this attack was a distributed denial-of-service (DDoS), a rudimentary yet often highly effective form of cyber warfare. A DDoS attack operates by overwhelming a target server, service, or network with a flood of illegitimate traffic from multiple compromised computer systems, collectively known as a botnet. This deluge of junk data exhausts the target’s bandwidth and processing capabilities, rendering it inaccessible to legitimate users.
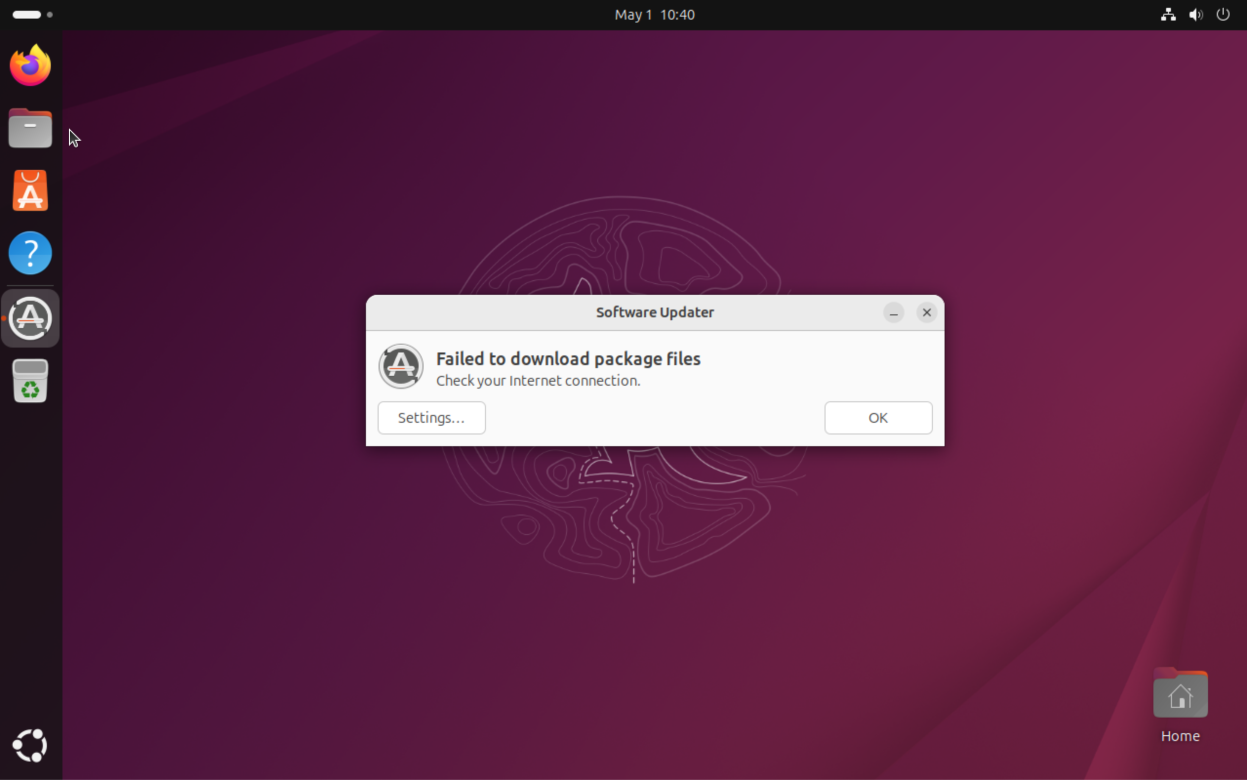
In the case of Ubuntu, the attack manifested as an inability for users to update and install software, alongside outages of several official Ubuntu and Canonical websites. Reports from unofficial Ubuntu community forums indicated that the attack specifically targeted Ubuntu’s security API, a critical component responsible for verifying software integrity and delivering security updates. This particular aspect of the attack is especially concerning, as it could potentially leave users vulnerable to other security threats by preventing them from receiving necessary patches. The incident’s duration, reportedly ongoing for approximately 20 hours at its peak, highlighted the sustained and determined nature of the assault. For end-users, this translated into frustrating "503 Service Unavailable" errors or unresponsive infrastructure, indicating that the servers were simply unable to handle the incoming requests.
The Rise of Hacktivism and Ideological Warfare
Responsibility for the extensive cyberattack was claimed by a group identifying itself as "The Islamic Cyber Resistance in Iraq 313 Team." This declaration, made via their Telegram channel, places the incident squarely within the realm of hacktivism – the act of using hacking techniques to promote a political or social cause. Hacktivist groups often leverage cyberattacks to draw attention to their grievances, disrupt services associated with perceived adversaries, or simply to demonstrate their capabilities.
The motivations behind such attacks are varied, ranging from political protest and ideological warfare to seeking notoriety or disrupting perceived symbols of Western influence. While the specific reasons for targeting Ubuntu remain speculative beyond the group’s general ideological stance, the choice of a widely used, globally recognized open-source platform suggests an intent to maximize disruption and visibility. Such attacks serve as a stark reminder that cyber warfare is not solely the domain of nation-states or sophisticated criminal organizations; ideologically driven groups, even with relatively unsophisticated tools, can significantly impact digital infrastructure and public services. The geopolitical landscape increasingly influences the cyber domain, leading to cross-border attacks that blur the lines between traditional conflict and digital disruption.
DDoS-for-Hire Services: Democratizing Cybercrime
A particularly troubling aspect of this incident is the perpetrators’ claim that they utilized "Beamed," a DDoS-for-hire service. These services, often referred to as "booters" or "stressers," significantly lower the barrier to entry for launching cyberattacks. They allow individuals or groups with minimal technical expertise to orchestrate powerful DDoS attacks by simply paying a fee. These platforms abstract away the complexities of managing botnets or generating high volumes of traffic, effectively "democratizing" access to cyber weaponry.
The scale of attacks facilitated by such services can be staggering. Beamed reportedly boasted capabilities of launching attacks exceeding 3.5 terabits per second (Tbps). To put this into perspective, a 3.5 Tbps attack represents an immense volume of data, equivalent to roughly half the bandwidth of what Cloudflare, a leading internet security company, described as the "largest DDoS attack ever recorded" at 7.3 Tbps. Such colossal traffic volumes highlight the immense strain these attacks place on network infrastructure and the sophisticated defenses required to mitigate them. The commercial availability of such powerful tools for malicious purposes represents a persistent challenge for cybersecurity professionals and law enforcement agencies globally.
Law Enforcement’s Uphill Battle Against Booter Services
The proliferation of DDoS-for-hire services has spurred a relentless "whack-a-mole" game for international law enforcement. Agencies like the U.S. Federal Bureau of Investigation (FBI) and Europol have made concerted efforts to dismantle these operations. Their strategies include seizing domains associated with booter websites, disrupting their payment processing channels, and, whenever possible, identifying and arresting the individuals behind these illicit platforms. These actions have seen varying degrees of success, with numerous services taken offline and perpetrators brought to justice.
However, the nature of the internet and the global reach of these services mean that as soon as one platform is shut down, others often emerge to fill the void. The operators frequently leverage anonymous payment methods, offshore hosting, and intricate networks to evade detection, making attribution and prosecution incredibly challenging. This ongoing cat-and-mouse game underscores the need for continuous international cooperation and advanced forensic capabilities to combat this persistent threat effectively. The social impact of these services is significant; they enable individuals to inflict real-world harm, economic disruption, and reputational damage without needing advanced technical skills, thereby lowering the ethical threshold for engaging in cybercrime.
Broader Implications for Digital Resilience and Trust
The attack on Ubuntu’s infrastructure carries significant implications beyond the immediate downtime. It serves as a stark reminder of the interconnectedness and fragility of our digital world. When a core operating system experiences such a widespread outage, the ripple effects can be substantial, impacting developers, businesses, and critical infrastructure that rely on Ubuntu. This incident underscores the paramount importance of robust cybersecurity measures, not just for proprietary software giants but for open-source projects that form the bedrock of much of the internet.
For the open-source community, incidents like this raise questions about resource allocation for security, particularly when compared to well-funded commercial entities. While open-source projects benefit from collective scrutiny and rapid patch deployment, they can also be attractive targets due to their widespread use. The incident also impacts user trust. Users expect reliable access to services and timely security updates. Disruptions to these fundamental aspects can erode confidence in the stability and security of the platform, potentially leading some to reconsider their choices, although Ubuntu’s strong community and track record of resilience often help mitigate such long-term effects.
In conclusion, the sustained DDoS attack against Ubuntu and Canonical represents more than just a temporary inconvenience. It is a potent illustration of the evolving cyber threat landscape, where hacktivism, facilitated by readily available cybercrime tools, can target foundational digital infrastructure. As organizations and individuals become increasingly reliant on digital services, the battle for cyber resilience — encompassing proactive defense, rapid incident response, and continuous vigilance — remains an ongoing and critical endeavor.