The digital infrastructure underpinning academic life for millions of students worldwide has been shaken anew, as education technology provider Instructure, the company behind the widely used Canvas learning management system, appears to have suffered a second cyber intrusion. This latest incident, following a recent disclosure of student data theft, involved the defacement of login portals for multiple educational institutions, displaying a ransom demand from the notorious cybercrime collective ShinyHunters. The escalating situation has intensified concerns over the security of sensitive educational data and the operational resilience of critical learning platforms.
The Digital Backbone of Modern Education: Instructure and Canvas
Instructure, a prominent player in the educational technology landscape, provides the Canvas platform, a comprehensive learning management system (LMS) utilized by K-12 schools, colleges, and universities globally. Canvas serves as a central hub for course management, assignment submissions, grading, and communication between educators and students. Its widespread adoption underscores the deep integration of digital tools into contemporary education, a trend significantly accelerated by the global shift to remote learning during the COVID-19 pandemic. Millions of users rely on Canvas daily for essential academic functions, making its integrity and security paramount to the continuity of education. The platform’s role as a digital lifeline means any compromise can have far-reaching consequences, disrupting learning, administrative processes, and eroding trust among its vast user base.
Initial Breach and Data Exfiltration
The current crisis for Instructure began with a data breach that the company publicly disclosed earlier in the week. In that incident, cybercriminals successfully infiltrated Instructure’s systems, illicitly accessing and exfiltrating a trove of private student information. The stolen data reportedly included sensitive details such as student names, personal email addresses, and the content of messages exchanged between teachers and students within the platform. The nature of this information raises significant privacy concerns, as personal identifiers can be exploited for various malicious activities, including identity theft, targeted phishing campaigns, and other forms of online fraud. The exposure of communications between educators and learners also infringes upon the privacy of academic discourse and personal interactions within the educational setting.
Following the initial breach, the ShinyHunters cybercrime group swiftly claimed responsibility, publicizing their alleged acquisition of data on their dedicated leak site. This tactic is a hallmark of financially motivated cyber extortion, where threat actors aim to pressure victim organizations into paying a ransom to prevent the public dissemination of stolen information. The group asserted that they had compromised data originating from nearly 9,000 schools across the globe, impacting an staggering 231 million individuals. While the full extent and verification of these claims remain under investigation, the sheer scale suggested by ShinyHunters painted a stark picture of the potential ramifications for the global education sector.
Escalation: Login Page Defacement and Direct Demands
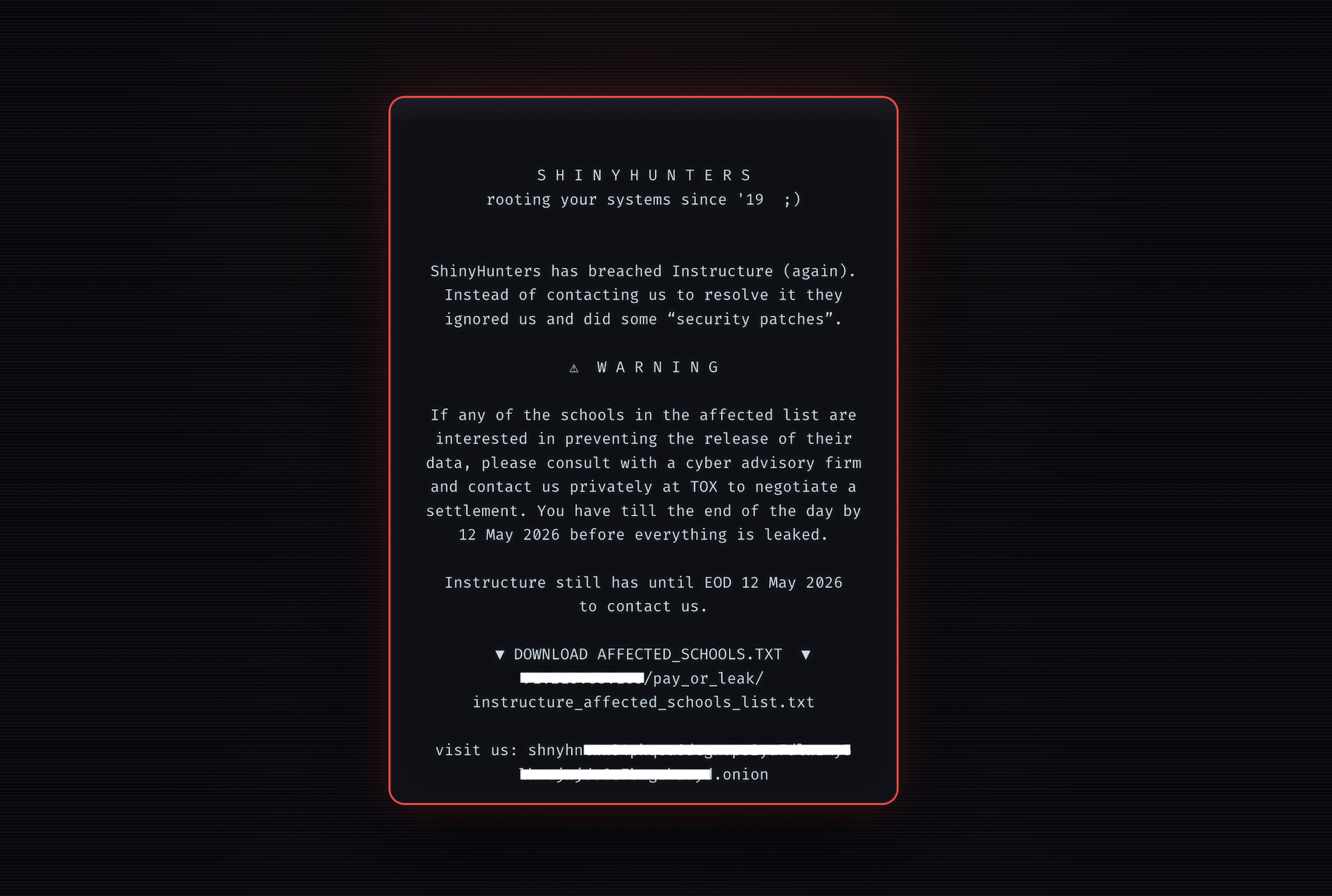
The situation took a more alarming turn when ShinyHunters reportedly executed a subsequent attack, this time targeting the public-facing login pages for Instructure’s Canvas platform. TechCrunch, a technology news outlet, observed that the login portals of at least three distinct educational institutions had been defaced. This act involved the injection of an HTML file that altered the standard login screens, replacing them with a message directly from the cybercrime group. The message explicitly stated ShinyHunters’ intent to publish the entirety of the previously stolen data on May 12, unless Instructure agreed to "negotiate a settlement." This direct, public ultimatum signifies a significant escalation in the pressure tactics employed by the attackers.
The immediate impact of the defacement was evident in the operational status of Instructure’s online presence. During the period of the reported defacement, Instructure’s primary website experienced intermittent availability, at times returning a "too many requests" error, suggesting potential distributed denial-of-service (DDoS) activity or system overload. Concurrently, the Canvas portal displayed a notice informing users that it was "currently undergoing scheduled maintenance." This message, while seemingly innocuous, often serves as a placeholder during emergency response or system recovery efforts following an unexpected incident. Instructure did not provide an immediate public comment regarding these developments, leaving many institutions and users seeking clarity and reassurance. A member of ShinyHunters, in communication with TechCrunch, indicated that the defacement represented a "second, separate breach," suggesting a distinct vector of compromise or an ongoing vulnerability that allowed for repeated access.
ShinyHunters: A Profile in Cyber Extortion
ShinyHunters is a well-established and notorious cybercrime organization known for its consistent and aggressive financially motivated attacks. Their operational playbook is characterized by a three-stage process: hack, publicize, and extort. The group typically gains unauthorized access to corporate networks, exfiltrates large volumes of sensitive data, and then publicly announces the breach on dark web forums or dedicated leak sites. This public disclosure serves a dual purpose: it pressures the victim organization by threatening reputational damage and regulatory fines, and it attracts potential buyers for the stolen data if the ransom demands are not met.
The decision by ShinyHunters to actively notify media outlets about the defaced login pages aligns perfectly with their strategy of maximizing pressure. By bringing public attention to the breach and the subsequent defacement, the group aims to amplify the reputational and operational consequences for Instructure and, by extension, its educational institution clients. This tactic seeks to compel the company to yield to their financial demands, leveraging the collective anxiety of millions of students, parents, and educators whose data and academic continuity are at stake. Their track record includes compromising numerous victims across various sectors over the past several years, consistently employing these high-pressure tactics.
Broader Implications for the Education Sector
The repeated targeting of Instructure highlights a disturbing trend: the increasing vulnerability of the education sector to sophisticated cyberattacks. Educational institutions, often operating with limited cybersecurity budgets and resources compared to corporate entities, have become attractive targets for cybercriminals. The vast amounts of personal data—from students’ academic records and health information to financial details—collected and stored by these institutions make them rich targets. Moreover, the critical role of LMS platforms like Canvas in daily academic operations means that successful attacks can cause widespread disruption, affecting learning outcomes, administrative efficiency, and institutional reputation.
The social and cultural impact of such breaches is profound. For students, the exposure of personal information can lead to long-term risks, including identity theft, financial fraud, and targeted harassment. Parents and guardians are increasingly concerned about the safety of their children’s data in digital learning environments. For educators and administrators, these incidents create an environment of distrust and anxiety, diverting valuable resources and attention away from core educational missions toward crisis management and enhanced security protocols. The psychological toll on individuals whose data has been compromised, particularly minors, is also a significant, though often unquantified, consequence.
The Cybersecurity Landscape and Vendor Responsibility
This incident also brings into sharp focus the complex challenges of securing a vast, interconnected digital ecosystem. As educational institutions increasingly rely on third-party vendors for critical services, the cybersecurity posture of these vendors becomes intrinsically linked to the overall security of the entire sector. A breach at a single provider like Instructure can have a cascading effect, potentially exposing data from thousands of client institutions. This highlights the concept of supply chain attacks, where attackers target a weaker link in the chain to gain access to multiple entities.
From an analytical perspective, Instructure faces an unenviable dilemma. Yielding to ransom demands can encourage further attacks and fund criminal enterprises, while refusing may lead to the public release of sensitive data, causing immense harm to individuals and institutions. Cybersecurity experts generally advise against paying ransoms, citing that it does not guarantee data recovery or prevent future breaches, and it legitimizes the criminal business model. However, the immense pressure of potential data exposure, especially when student data is involved, can make this a difficult decision for any organization.
The "too many requests" error and "scheduled maintenance" notices observed during the defacement could indicate Instructure’s rapid response efforts, including attempting to mitigate a DDoS attack or taking systems offline for emergency patching and forensic analysis. Such actions are standard in incident response but also underscore the severity and immediate nature of the threat.
The ongoing incident serves as a critical reminder for all stakeholders in the education sector about the imperative for robust, multi-layered cybersecurity defenses. This includes not only technical safeguards but also comprehensive incident response plans, continuous security audits, and proactive threat intelligence sharing. Furthermore, there is an increasing demand for greater transparency and accountability from education technology vendors regarding their security practices and their handling of sensitive data. As the digital transformation of education continues, so too must the evolution of its security infrastructure to protect the millions who rely on it. The outcome of Instructure’s current predicament with ShinyHunters will likely set precedents and influence future strategies in the ongoing battle against cybercrime in the academic world.