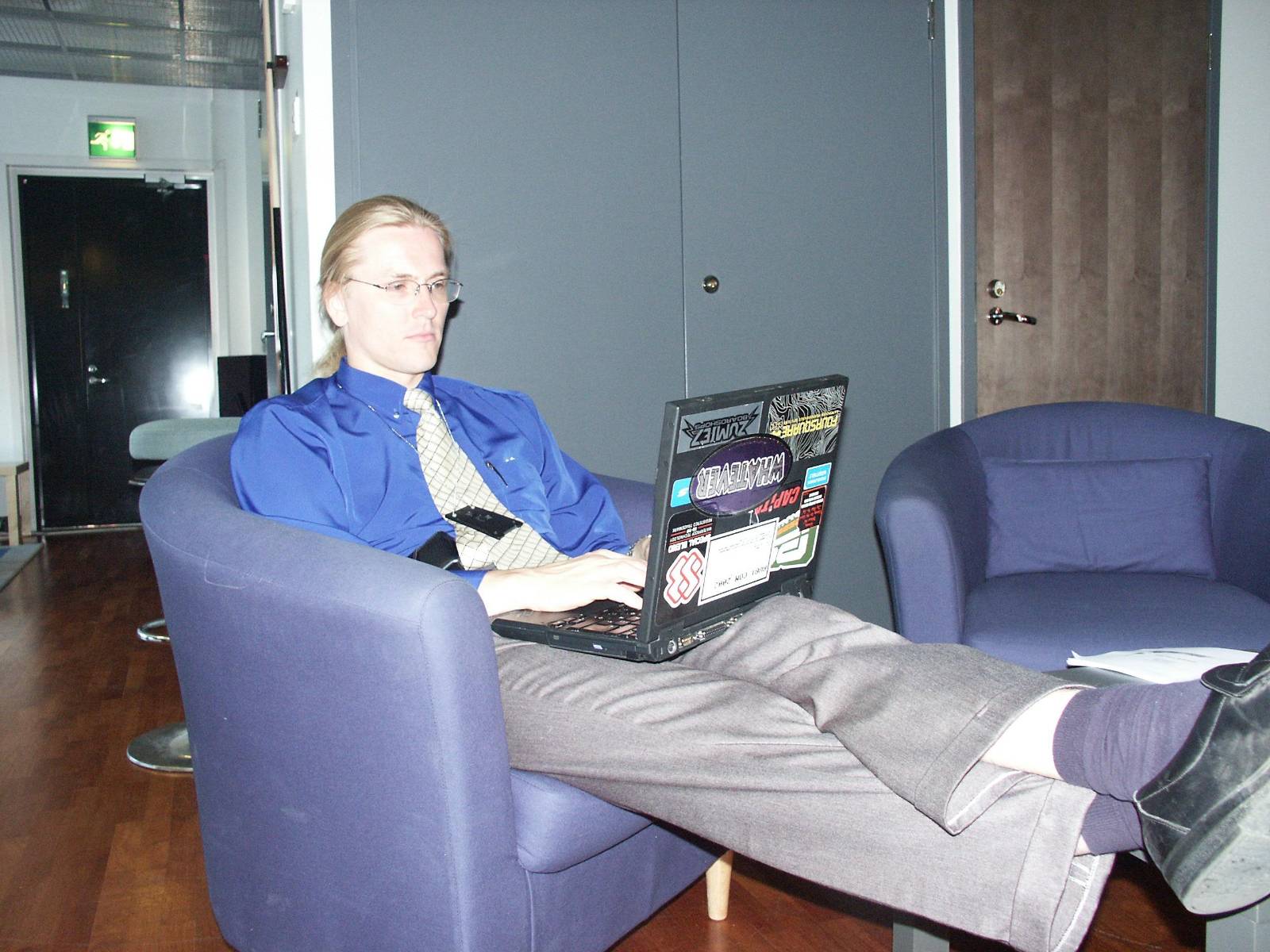
Mikko Hyppönen, a towering figure in the global cybersecurity community, commanded the stage with his characteristic blend of calm authority and engaging wit. Dressed in an immaculate teal suit, his dark blonde ponytail a familiar sight, he articulated a profound observation to a packed auditorium of fellow experts and researchers at a prominent industry gathering in Las Vegas. He likened the relentless struggle against digital threats to a game of "cybersecurity Tetris," a metaphor that resonated deeply with his audience. In this digital analogy, successful defenses, like completed lines of bricks, vanish without a trace, leaving behind only the accumulating failures.
"Your successes disappear, while your failures pile up," he explained during his keynote address at Black Hat in 2025, underscoring a core paradox of the profession. "The challenge we face as cybersecurity people is that our work is invisible… when you do your job perfectly, the end result is that nothing happens." This sentiment captures the often-unseen vigilance required to protect the interconnected world, a vigilance Hyppönen has personified for over three and a half decades.
A Legacy Forged in the Digital Wild West
Hyppönen’s career, spanning more than 35 years, has been anything but invisible. Since the late 1980s, he has been at the vanguard of the fight against malicious software, witnessing the nascent stages of what would become a pervasive global threat. When he began, terms like "malware" were not yet part of the common lexicon; instead, digital threats were known primarily as "computer viruses" or "Trojans." The internet was a nascent concept, accessible to only a privileged few, and the primary vector for contagion was often the humble floppy disk. Early viruses, like the notorious Brain virus of 1986, spread via these physical storage devices, passed between computers in a chain reaction, long before global networks facilitated instant transmission.
His journey into cybersecurity began with a youthful fascination for hacking video games on the Commodore 64, a popular home computer of the era. This early curiosity evolved into a sophisticated skill set as he delved into reverse engineering, initially to bypass anti-piracy protections. He honed his coding abilities by developing adventure games, a foundation that proved invaluable when he joined Data Fellows, a Finnish company that would later become the renowned antivirus firm F-Secure. It was there that Hyppönen applied his reverse engineering prowess to dissect and understand the burgeoning world of computer viruses, laying the groundwork for his legendary career. Over the years, he has personally analyzed thousands of distinct strains of malware, becoming one of the most recognizable and respected voices in the cybersecurity community through his frequent global conference appearances.
From Hobbyist Code to Global Cyberwarfare
The landscape of malicious software has undergone a dramatic transformation since Hyppönen first started. In the early days, virus writers were often driven by intellectual curiosity, a desire to test the boundaries of code, or simply to make a statement. Monetization was largely an unexplored avenue; the infrastructure for large-scale financial exploitation – such as readily available cryptocurrencies for extortion or robust criminal marketplaces for stolen data – simply didn’t exist.
Consider the Form.A virus, a prevalent threat in the early 1990s. This floppy disk-borne infection typically caused minimal damage, sometimes merely displaying a message on the screen. Yet, its ability to travel globally, even reaching remote research stations in Antarctica, underscored the inherent vulnerability of interconnected systems, even in their infancy.
The turn of the millennium marked a significant shift with the emergence of "wormable" threats, designed to self-replicate and spread rapidly across networks. Hyppönen and his colleagues at F-Secure were among the first to identify the infamous ILOVEYOU worm in 2000. This highly destructive piece of malware arrived as an email attachment disguised as a love letter. If opened, it would overwrite and corrupt files on the victim’s computer before automatically forwarding itself to everyone in their contact list. The ILOVEYOU worm crippled systems worldwide, infecting over 10 million Windows computers and causing billions of dollars in damage, a stark illustration of the escalating potential for digital disruption. Its impact was so profound that it led to widespread changes in email security protocols and increased public awareness of cyber threats.
Today, the era of hobbyist virus writing is largely a relic of the past. The development of malicious software is almost exclusively driven by financial gain, state-sponsored espionage, or the shadowy world of mercenary spyware. Modern malware authors are sophisticated operators, focused on stealth and persistence. Self-spreading worms, once common, are now rare exceptions, as they are quickly detected and neutralized by advanced cybersecurity defenses, often leading to the identification of their creators. Notable exceptions like the WannaCry ransomware attack by North Korea in 2017, which leveraged a vulnerability to spread globally and demand ransom in Bitcoin, and Russia’s NotPetya campaign later that year, which devastated Ukraine’s infrastructure and caused collateral damage worldwide, highlight the continued destructive potential of such methods when wielded by state actors.
The cybersecurity industry itself has matured dramatically. From a collection of enthusiasts sharing free tools, it has evolved into a professionalized, multi-billion dollar sector, estimated to be worth approximately $250 billion. This growth is a direct response to the escalating sophistication and volume of cyberattacks. Furthermore, consumer devices, particularly smartphones like the iPhone, have become remarkably secure. Exploits for these platforms or for widely used browsers like Chrome now command six-figure or even multi-million dollar prices in the black market. This exorbitant cost effectively limits their use to highly resourced state actors, making them largely inaccessible to financially motivated cybercriminals. This represents a significant victory for consumers and a testament to the effectiveness of the cybersecurity industry’s efforts.
A New Battlefield: From Digital Packets to Drone Protocols
Despite the advancements in traditional cybersecurity, Hyppönen recognized a new frontier emerging, one with profound implications for global security. In mid-2025, he made a decisive pivot, transitioning from the established world of malware defense to a burgeoning domain: countering unmanned aerial vehicles (UAVs), commonly known as drones. He assumed the role of Chief Research Officer at Sensofusion, a Helsinki-based company specializing in anti-drone systems for military and law enforcement agencies.
This shift was deeply personal and geopolitically motivated. As a Finnish citizen living just two hours from his country’s border with Russia, Hyppönen is acutely aware of regional tensions. Finland, with its long history of confronting its powerful eastern neighbor, shares a collective memory of conflict, a sentiment reinforced by his grandfathers’ service against Russian forces. The 2022 full-scale invasion of Ukraine, where unmanned aerial attacks have reportedly accounted for a significant majority of casualties, served as a stark demonstration of drones’ transformative role in modern warfare. This conflict underscored the urgent need for robust counter-drone capabilities, pushing Hyppönen to seek a renewed impact in a field where the defensive aspects remain largely uncharted territory.
"The situation is very, very important to me," Hyppönen stated, emphasizing the personal conviction behind his career change. "It’s more meaningful to work fighting against drones, not just the drones that we see today, but also the drones of tomorrow. We’re on the side of humans against machines, which sounds a little bit like science fiction, but that’s very concretely what we do."
Parallels in Defense: Signatures, Frequencies, and the Adversarial Dance
While the realms of cybersecurity and drone technology might appear disparate, Hyppönen identifies striking parallels in their defensive strategies. Just as cybersecurity companies develop "signatures" to identify, detect, and block malicious software, drone defense involves creating systems that can pinpoint, track, and neutralize hostile UAVs. This often entails jamming their radio frequencies or analyzing their unique "IQ samples" – the raw radio frequency data that allows for the precise identification of a drone’s communication protocol.
By recording and analyzing these radio frequencies, defenders can build a library of signatures for known drone models and, crucially, develop methods to detect unknown or novel drones. Once the communication protocol and frequencies are identified, it opens the door to protocol-level cyberattacks against the drone itself. This could involve sending malformed commands or exploiting vulnerabilities in its control system, potentially causing it to malfunction, crash, or even be taken over. "So in many ways, these protocol level attacks are much, much easier in the drone world because the first step is the last step," Hyppönen noted. "If you find a vulnerability, you’re done." This highlights the often-binary nature of drone vulnerabilities compared to the layered defenses of complex software systems.
The fundamental "cat-and-mouse game" that defines cybersecurity also permeates the world of drone warfare. Defenders develop new methods, adversaries adapt, and the cycle of innovation and counter-innovation continues relentlessly. This constant escalation mirrors the historical trajectory of malware evolution, where each defensive breakthrough prompts new offensive tactics.
Perhaps the most poignant continuity for Hyppönen lies in the identity of the adversary. "I spent a big part of my career fighting against Russian malware attacks," he reflected. "Now I’m fighting Russian drone attacks." This statement encapsulates the enduring nature of geopolitical tensions manifesting across different technological battlegrounds. For a veteran like Mikko Hyppönen, the tools and targets may evolve, but the core mission of defense, whether against digital intrusions or aerial threats, remains constant. His journey underscores a critical trend: as technology advances, the boundaries between traditional warfare and cyber warfare continue to blur, demanding a new generation of defenders capable of navigating both the digital and physical domains.