The digital realm, constantly expanding, harbors immense repositories of malicious software, a stark testament to the persistent and evolving threat landscape. Comprehending the sheer volume of these digital arsenals can be challenging, often transcending abstract numerical figures. Two prominent entities in the cybersecurity world, vx-underground and VirusTotal, recently offered a glimpse into the colossal scale of their respective malware collections, prompting a unique physical visualization that brings these abstract numbers into tangible perspective.
The Digital Hoards: Two Key Players
vx-underground, a prominent malware research collective, recently disclosed its possession of an estimated 30 terabytes of malware source code, claiming it to be the world’s most extensive repository of its kind. This specialized group acts as a vital digital library for cybersecurity researchers, providing access to the raw blueprints and underlying code of malicious programs. Its mission is to facilitate a deeper understanding of cyber threats by making actual malware components available for analysis under controlled conditions, fostering advanced research into their design and functionality.
Bernardo Quintero, founder of VirusTotal, an online service renowned for scanning files across numerous antivirus engines, subsequently revealed an even more staggering figure: his platform hosts approximately 31 petabytes of user-contributed malware samples. For immediate context, one petabyte is roughly equivalent to 1,024 terabytes, meaning VirusTotal’s collection is orders of magnitude larger than vx-underground’s. VirusTotal, a subsidiary of Google, operates as a crucial public service, enabling users globally to upload suspicious files or URLs for comprehensive analysis across a multitude of security vendors simultaneously. This crowdsourced approach allows for rapid identification of emerging threats and facilitates unparalleled threat intelligence sharing across the cybersecurity ecosystem. The distinction between vx-underground’s focus on source code and VirusTotal’s emphasis on executable samples is important; the former provides insight into creation, while the latter offers a vast collection of operational malware.
Why Such Vast Archives Matter
These immense data repositories are far from mere digital curiosities; they form the bedrock of modern cybersecurity defense. Cybersecurity companies, artificial intelligence researchers, and threat intelligence firms consider these archives indispensable tools in their ongoing battle against cyber adversaries.
Background Context for Cyber Defense
Access to diverse and extensive datasets of malware is critical for training sophisticated detection models that can identify both known and novel threats. Researchers utilize these archives to reverse-engineer malicious software, meticulously dissecting its functionality, identifying its command-and-control infrastructure, and understanding its propagation methods. This detailed analysis helps in developing effective countermeasures and patching vulnerabilities. Furthermore, these repositories enable security experts to track the evolution of attack methodologies, anticipate future threat vectors, and stay ahead of constantly adapting cybercriminals. Without such comprehensive access, defenders would be perpetually reacting to threats rather than proactively mitigating them.
Market and Economic Impact
The global cybersecurity market, valued at hundreds of billions of dollars annually, is primarily driven by the relentless proliferation and increasing sophistication of cyber threats. Companies across all sectors invest heavily in research and development to create more robust security solutions. Access to vast malware libraries allows these firms to develop and refine antivirus software, intrusion detection and prevention systems, endpoint detection and response (EDR) tools, and advanced threat hunting platforms. The economic cost of cybercrime is staggering, estimated to be in the trillions of dollars globally each year, impacting businesses, governments, and individuals. Effective cybersecurity, underpinned by comprehensive threat intelligence derived from these archives, directly mitigates these financial damages. Moreover, the sharing of threat intelligence, often facilitated by platforms like VirusTotal, fosters a collaborative defense ecosystem, elevating the baseline security posture across various industries and nations.
Social and Cultural Repercussions
Beyond the financial implications, malware profoundly impacts daily life and societal stability. Ransomware attacks can cripple critical infrastructure, from hospitals disrupting patient care to municipal services grinding to a halt. Data breaches expose sensitive personal information, leading to identity theft, financial fraud, and a pervasive erosion of trust in digital services. Nation-state-sponsored malware can destabilize geopolitical relations, interfere with democratic processes, and compromise critical national assets like power grids and financial systems. The increasing global dependence on digital technologies means that the integrity and security of our online environments are paramount. The diligent collection and study of these malware archives are therefore vital not just for safeguarding corporate assets, but for protecting individual privacy, public safety, and the foundational stability of modern society.
A Historical Perspective on Digital Threats
The evolution of malware mirrors the progression of computing technology itself, growing in complexity and pervasiveness over decades.
Timeline of Malware Evolution
The journey of malware began modestly in the 1970s with experimental programs like the "Creeper" virus, an early self-replicating program. The 1980s saw the emergence of the first widely recognized personal computer viruses, such as "Elk Cloner" for Apple II and "Brain" for IBM PCs, often spread via floppy disks. The 1990s brought forth polymorphic viruses, which could change their code to evade detection, and macro viruses, which leveraged Microsoft Office documents, signifying a shift towards more sophisticated evasion techniques and wider distribution channels.
The early 2000s were dominated by fast-spreading internet worms like "Code Red" and "SQL Slammer," capable of crippling networks globally within minutes by exploiting software vulnerabilities. This era also marked the rise of trojans, malicious programs disguised as legitimate software, facilitating remote access, data theft, and the creation of botnets. The 2010s ushered in the age of sophisticated ransomware, exemplified by "CryptoLocker" and "WannaCry," which encrypt victims’ data and demand payment for its release. Concurrently, Advanced Persistent Threats (APTs) emerged – highly targeted, stealthy attacks often attributed to nation-states or organized criminal groups, focused on long-term espionage or sabotage. Today, malware development continues to accelerate, with new variants constantly emerging, often leveraging artificial intelligence and machine learning to become more evasive, potent, and customized.
Evolution of Cyber Defense
In parallel with malware’s evolution, cybersecurity defenses have undergone a radical transformation. Early defenses relied on simple signature-based antivirus programs that identified known malware patterns. As malware became polymorphic, fileless, and more evasive, behavioral analysis, heuristics, and sandboxing became crucial, allowing systems to detect suspicious activities rather than just known signatures. Today, the landscape is dominated by multi-layered, AI-driven solutions. Threat intelligence platforms aggregate and analyze vast amounts of data, while Endpoint Detection and Response (EDR) systems monitor device activity for anomalies. Security Information and Event Management (SIEM) tools correlate security events across entire networks, providing a holistic view of an organization’s security posture. Cloud-based security solutions offer scalable protection. The reliance on immense datasets of both malicious and benign files for training machine learning models is a defining characteristic of modern defense, enabling systems to predict and detect novel threats with greater accuracy.
The Challenge of Visualization: From Bits to Buildings
Conceptualizing abstract data volumes, especially those reaching terabytes and petabytes, often proves challenging for the human mind. While cybersecurity professionals regularly grapple with such figures, translating them into a tangible, relatable scale can illuminate their true magnitude for a broader audience. A common pitfall in this endeavor is relying solely on computational tools without critical human oversight; for instance, some artificial intelligence chatbots, when asked to visualize such data, have produced wildly inaccurate physical representations, underscoring the need for careful, empirical calculation. To bridge this gap between abstract numbers and physical reality, a simplified, yet illustrative, calculation can be immensely helpful.
The Physical Manifestation: Stacks of Drives
To create a concrete visualization, we can imagine these digital archives stored on standardized physical hard drives.
Methodology for Physical Scale
For this exercise, we will consider widely available 3.5-inch internal hard drives, commonly found in desktop computers. These drives are typically designed to consistent physical dimensions, with a height of approximately one inch. We will assume a capacity of exactly 1 terabyte per drive for straightforward calculation, acknowledging that actual usable capacity might be slightly less due to formatting overheads and that drive capacities have grown significantly beyond 1TB in real-world scenarios. This approach provides a clear, consistent unit for comparison, focusing purely on the physical volume required for the data.
vx-underground’s Archive in Hard Drives
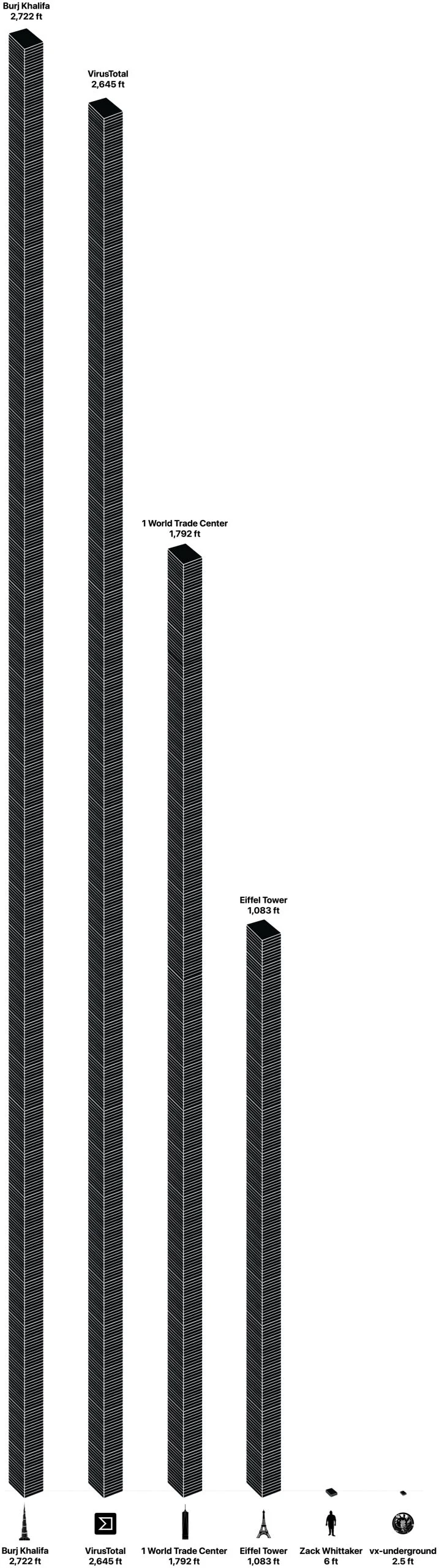
vx-underground’s collection of 30 terabytes, when hypothetically stored on 30 individual 1-terabyte hard drives, would result in a stack reaching 30 inches, or precisely 2.5 feet in height. To put this into perspective, this stack would be approximately half the height of an average adult. While significant for a specialized archive, especially one focused on source code, it remains relatively modest when compared to larger data aggregations.
VirusTotal’s Colossal Collection in Hard Drives
The scale shifts dramatically when considering VirusTotal’s 31 petabytes of user-contributed malware samples. Converting petabytes to terabytes (31 PB = 31,744 TB, using 1 PB = 1024 TB for precision in data storage), this would necessitate approximately 31,744 individual 1-terabyte hard drives. Stacked one on top of the other, each measuring one inch in height, this digital edifice would ascend to an astonishing 31,744 inches. This translates to roughly 2,645 feet.
To truly grasp this immense scale, consider some of the world’s most iconic structures. The Eiffel Tower in Paris stands at 1,083 feet, including its antenna. VirusTotal’s malware data, physically stacked, would therefore be more than twice the height of the Eiffel Tower, approaching two-and-a-half times its stature. Even the majestic Burj Khalifa in Dubai, currently the world’s tallest building at 2,722 feet, would be only marginally taller than this hypothetical tower of malware data. This striking comparison vividly underscores the truly monumental scale of information collected in the ongoing, dynamic battle against cyber threats.
Neutral Analytical Commentary: The Ever-Growing Digital Threat Landscape
The sheer volume of malware data housed by organizations like vx-underground and VirusTotal serves as a stark indicator of the relentless and escalating cyber threat landscape. This continuous growth is fueled by several critical factors: the increasing sophistication and global reach of cybercriminal syndicates, the proliferation of readily available exploit kits and malware-as-a-service offerings on dark web markets, and the automation of malware generation processes. The "arms race" between attackers and defenders is perpetual, with each innovation on one side prompting a counter-innovation on the other.
The role of artificial intelligence and machine learning in this dynamic is dual-edged. While these technologies are increasingly leveraged by cybersecurity firms to detect anomalies, predict attack vectors, and automate defense responses, they are also being exploited by malicious actors. AI can be used to generate highly evasive malware, craft hyper-realistic phishing campaigns, and automate reconnaissance, further complicating detection efforts. This constant escalation necessitates ever-larger datasets for training defensive AI models, creating a feedback loop where more threats lead to more data, which in turn is needed to combat more threats.
Furthermore, these vast repositories highlight the critical importance of collaboration within the cybersecurity community. Platforms like VirusTotal exemplify how collective intelligence, derived from millions of user submissions, can create a powerful defense mechanism that no single entity could achieve alone. The ongoing commitment to collecting, analyzing, and sharing threat intelligence is paramount to maintaining a resilient digital ecosystem against an adversary that is global, agile, and increasingly potent. The physical visualization of these digital threats underscores the tangible impact of an otherwise abstract problem, reminding us of the immense effort required to secure our interconnected world.
Conclusion
The efforts of organizations like vx-underground and VirusTotal in meticulously curating and analyzing enormous volumes of malware data are fundamental to global cybersecurity. While the abstract numbers — 30 terabytes for source code and an astounding 31 petabytes for samples — are challenging to fully comprehend, their translation into physical stacks of hard drives offers a vivid and sobering illustration. Imagine a tower of hard drives rivaling the Burj Khalifa in height; this is the physical representation of the digital battleground. These monumental archives are not just collections of malicious code; they are indispensable libraries for understanding, predicting, and ultimately defending against the ever-present and ever-evolving specter of cyber threats, underscoring the relentless human endeavor to safeguard the digital frontier for a more secure future.