A U.S. judge has ordered Peter Williams, a former top cybersecurity executive at defense contractor L3Harris, to pay an additional $10 million in restitution to his former employer. This significant financial penalty comes on top of $1.3 million Williams was previously mandated to pay, stemming from his central role in one of the most severe leaks of advanced hacking tools in the history of the United States and its closest intelligence allies. The ruling underscores the profound financial and national security repercussions of Williams’s actions, which involved pilfering highly sensitive cyber exploits and selling them to a Russian-affiliated broker.
The Architect of the Breach
Peter Williams, a 39-year-old Australian citizen, once held a position of immense trust and responsibility as the general manager of Trenchant, L3Harris’s elite division specializing in sophisticated spyware and offensive cyber tools. Before his tenure at the U.S. defense giant, Williams honed his skills within one of Australia’s intelligence agencies, accumulating expertise that positioned him at the vanguard of cybersecurity development. His professional background provided him with unparalleled access to some of the most guarded digital weaponry developed for Western intelligence and defense operations. This deep understanding of both offensive cyber capabilities and the intelligence landscape made his subsequent betrayal all the more alarming, highlighting the critical vulnerabilities inherent in insider threats, even within the most secure environments. The trust placed in individuals with such specialized knowledge is paramount, and Williams’s actions represent a profound breach of that trust, impacting not just a single corporation but the broader national security framework.
Trenchant and the Five Eyes Alliance
Trenchant emerged from the strategic acquisition of two sister startups, consolidating advanced capabilities under the L3Harris umbrella. Its primary mission was to develop cutting-edge cyber exploits and surveillance technologies exclusively for the U.S. government and its partners within the Five Eyes intelligence alliance. This powerful coalition, comprising the United States, Australia, Canada, New Zealand, and the United Kingdom, represents a cornerstone of global intelligence sharing among English-speaking democracies. The tools crafted by Trenchant are not merely digital instruments; they are crucial assets in intelligence gathering, counter-terrorism, and cyber warfare, designed to provide strategic advantages in an increasingly complex global threat landscape.
These tools often leverage "zero-day" vulnerabilities—flaws in software or hardware previously unknown to the vendor, offering a critical window for exploitation before patches can be developed. The ability to discover, develop, and deploy such exploits is a highly specialized and expensive endeavor, representing years of research and development. Their value lies in their stealth and effectiveness, making them indispensable for intelligence agencies seeking to access adversary networks or gather critical information without detection. A leak of such instruments directly compromises the operational capabilities of the Five Eyes nations, potentially exposing their methods, targets, and even their own vulnerabilities to hostile state actors. The very existence of the Five Eyes alliance is predicated on mutual trust and the secure sharing of sensitive information, making a breach of this nature particularly damaging to the fabric of international cooperation.
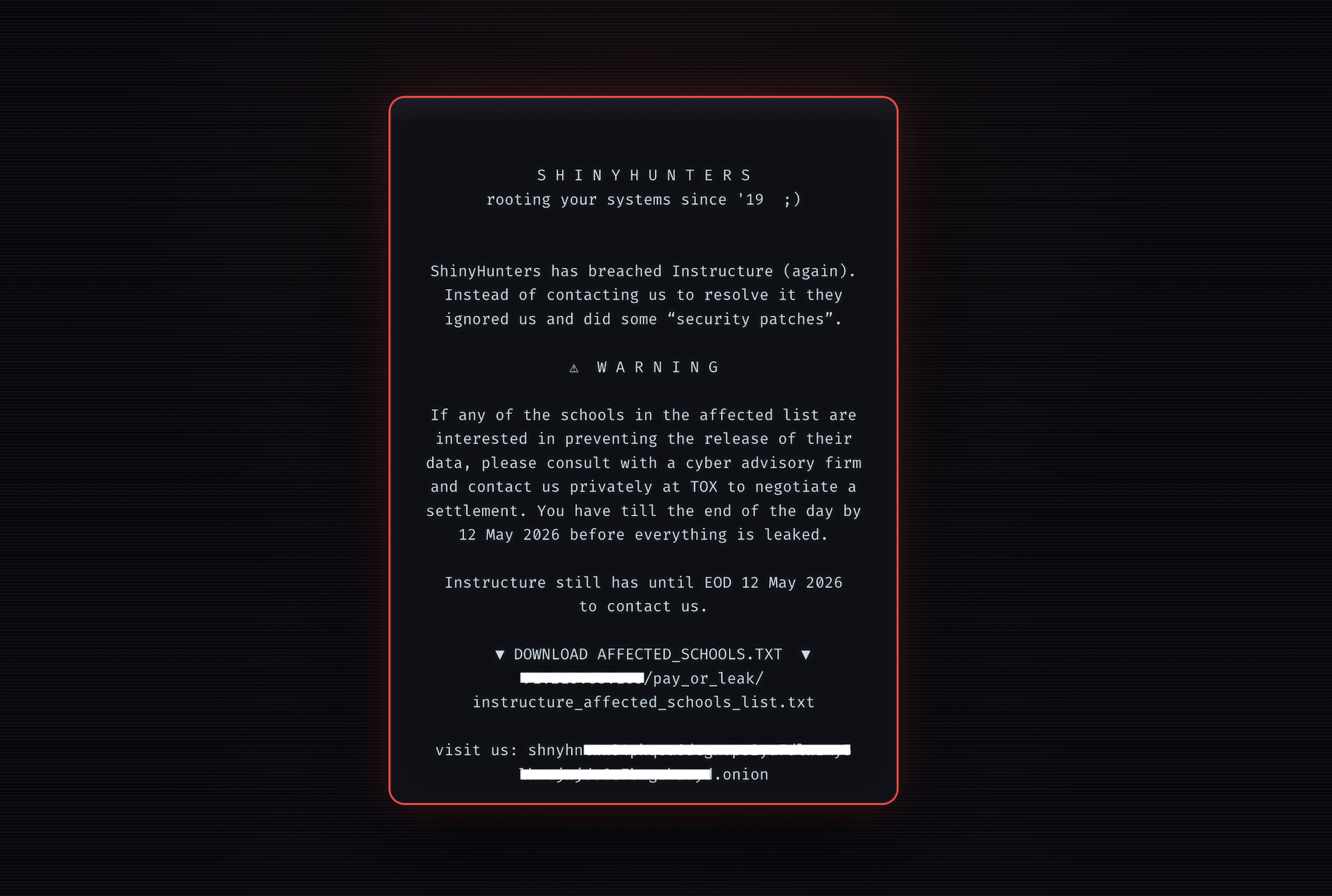
The Lure of the Exploit Market
The global market for cyber exploits, particularly zero-day vulnerabilities, is a shadowy but lucrative one, driven by nation-states, intelligence agencies, and even sophisticated criminal organizations. Brokers like Operation Zero, the Russian firm to whom Williams sold the stolen tools, act as intermediaries, connecting exploit developers with buyers willing to pay exorbitant sums for exclusive access to potent cyber weapons. Operation Zero explicitly states its allegiance, claiming to work solely with the Russian government and local companies, raising immediate red flags regarding the ultimate destination and use of any acquired tools.
The proliferation of these digital weapons, often developed with taxpayer money for defensive purposes, into the hands of potentially adversarial nations represents a critical challenge to international stability. The market dynamics incentivize the discovery and weaponization of vulnerabilities, creating a continuous arms race in the cyber domain. For individuals like Williams, the temptation of immense personal wealth can outweigh the ethical and national security implications. The sums offered for high-value exploits can dwarf conventional salaries, creating a powerful incentive for betrayal. This commercialization of cyber warfare tools blurs the lines between state-sponsored espionage and purely mercenary actions, complicating efforts to track attribution and hold perpetrators accountable in the global arena.
A Calculated Betrayal and its Unfolding
Williams’s scheme was meticulously planned, exploiting his "full access" to Trenchant’s internal networks to siphon off seven unspecified trade secrets. These secrets were almost certainly highly valuable cyber exploits—code designed to hijack software vulnerabilities—and sophisticated surveillance technology. The motivation, as revealed in court proceedings, was financial gain. Williams reportedly made $1.3 million from the sale, using the illicit proceeds to fund a lavish lifestyle that included luxury watches, a house near Washington D.C., and family vacations.
The unraveling of Williams’s deception began with his arrest and subsequent accusation of stealing trade secrets in late 2025. Facing overwhelming evidence, he pleaded guilty to the charges, acknowledging the gravity of his actions. In early 2026, a judge sentenced him to more than seven years in prison, marking a severe consequence for his betrayal. However, the financial cost to L3Harris far exceeded Williams’s personal enrichment. Prosecutors were informed by Trenchant that the company suffered estimated losses of up to $35 million due to Williams’s theft. This figure likely encompasses not only the direct value of the stolen intellectual property but also the costs associated with investigating the breach, remediating compromised systems, developing new tools to replace those potentially neutralized, and significant reputational damage within the defense community. Compounding his perfidy, Williams even attempted to frame one of his employees for the theft, a desperate act to deflect suspicion and escape accountability.
Far-Reaching Geopolitical Consequences
The U.S. government swiftly condemned Williams’s actions, with prosecutors asserting that he "betrayed" the United States and its allies. They characterized Operation Zero as "one of the world’s most nefarious exploit brokers," highlighting the critical danger posed by the stolen tools. These tools, according to the Department of Justice, possessed the capability to compromise "millions of computers and devices around the world," underscoring the vast potential for destructive or disruptive use.
The fears surrounding the tools’ deployment were not unfounded. Subsequent cybersecurity research published by Google, investigating cyberattacks, revealed that some of the stolen exploits were indeed deployed in the wild. Former L3Harris employees, recognizing the distinctive code, identified these tools as originating from Trenchant. Alarming reports indicated that these advanced hacking capabilities were initially leveraged by Russian government spies operating in Ukraine, a critical theater of ongoing geopolitical conflict. Later, the same tools were found in the hands of Chinese cybercriminals, illustrating the dangerous proliferation effect of such leaks. This trajectory from a U.S. defense contractor to Russian intelligence and then to Chinese criminal elements underscores the severe and unpredictable geopolitical fallout of insider espionage. It not only compromises current intelligence operations but also provides adversaries with insights into the capabilities and methodologies of Western cyber defenses, potentially forcing a costly and time-consuming overhaul of security postures.
The Enduring Threat of Insider Espionage
The case of Peter Williams serves as a stark reminder of the persistent and complex challenge posed by insider threats to national security and corporate integrity. While organizations invest heavily in perimeter defenses and advanced cybersecurity measures to ward off external attackers, the human element remains a critical vulnerability. Individuals with privileged access, driven by financial desperation, ideological motives, or personal grievances, can circumvent even the most robust technical safeguards.
Analytical commentary often highlights that the damage from an insider breach can be far more extensive than an external attack, as the insider already possesses knowledge of internal systems, vulnerabilities, and strategic assets. This incident will undoubtedly prompt a re-evaluation of security protocols within the defense industrial base, emphasizing enhanced vetting, continuous monitoring of employee behavior, and more stringent access controls based on the principle of least privilege. Beyond the immediate legal and financial ramifications, the Williams case contributes to a broader understanding of the evolving landscape of cyber warfare, where the lines between state-sponsored operations, criminal enterprises, and individual opportunism can become dangerously blurred, demanding ever more sophisticated and holistic security strategies.
Financial Repercussions and Legal Closure
The latest court order for Williams to pay an additional $10 million in restitution brings the total amount he is legally obligated to repay L3Harris to $11.3 million. This substantial sum reflects the court’s acknowledgment of the extensive financial damage suffered by the defense contractor, which estimated its losses at up to $35 million. While it is unlikely that L3Harris will fully recover its losses, the restitution order sends a clear message about the severe consequences awaiting individuals who exploit their positions of trust for personal gain at the expense of national security.
The legal proceedings have now largely concluded with both a prison sentence and significant financial penalties for Williams. His journey from a respected cybersecurity executive within the Five Eyes intelligence community to a convicted felon and a debtor facing multi-million dollar restitution serves as a cautionary tale. It underscores the profound and far-reaching impact of individual choices within the high-stakes world of national security, where a single act of betrayal can have reverberations across international alliances and compromise critical defense capabilities for years to come.