The digital frontier of artificial intelligence, a realm often characterized by rapid innovation and collaborative development, recently became the stage for a real-world cybersecurity incident that could easily be mistaken for a plotline from a tech satire. A prominent open-source project, LiteLLM, designed to streamline access to a multitude of AI models, fell victim to a sophisticated malware attack this week. This breach not only highlighted the inherent vulnerabilities within the modern software supply chain but also cast a shadow over the efficacy of certain security compliance certifications, particularly those provided by the startup Delve, which has itself faced scrutiny.
The Breach: How a Critical AI Tool Was Compromised
LiteLLM, a graduate of the prestigious Y Combinator accelerator, has emerged as a significant player in the burgeoning AI landscape. It offers developers a unified interface to interact with hundreds of diverse AI models, providing essential functionalities like expenditure management. Its utility has garnered immense popularity, reportedly reaching download figures as high as 3.4 million times daily, according to insights from cybersecurity firm Snyk. With a robust presence on GitHub, boasting tens of thousands of stars and numerous forks, LiteLLM underpins a substantial segment of AI development, making its compromise particularly concerning.
The malicious software found its way into LiteLLM through a "dependency" – a common term in software development referring to external code packages that a project relies upon to function. Modern software applications are rarely built from scratch; instead, they integrate numerous pre-existing libraries and modules, many of which are open source. This interconnectedness, while fostering rapid development and innovation, simultaneously creates a vast attack surface. In this instance, the malware exploited this intricate web, infiltrating LiteLLM via one of its foundational components. Once embedded, its primary objective was to steal login credentials, enabling it to propagate further by accessing more open-source packages and user accounts, thereby harvesting an ever-widening array of sensitive data.
The discovery of the malware was a stroke of fortunate happenstance, meticulously documented and disclosed by research scientist Callum McMahon of FutureSearch, a company specializing in AI agents for web research. McMahon’s investigation was prompted by an unexpected system shutdown on his machine shortly after downloading LiteLLM. This unusual event triggered a deeper dive, leading to the uncovering of the malicious code. Ironically, it was a flaw within the malware itself – described by McMahon and other prominent AI researchers as "sloppily designed" or "vibe coded," implying a lack of professional rigor in its construction – that caused his system to crash, inadvertently exposing its presence. The LiteLLM development team responded with commendable speed, working tirelessly to contain and rectify the situation, with initial reports suggesting the breach was detected and addressed within hours.
The Expanding Threat of Software Supply Chain Attacks
The LiteLLM incident serves as a stark reminder of the escalating threat of software supply chain attacks, a category of cyber warfare that has grown increasingly prevalent and sophisticated. Unlike traditional attacks that target an organization’s perimeter, supply chain attacks compromise a legitimate component of the software development process, often an open-source library, a build tool, or even an update mechanism. This allows attackers to inject malicious code into trusted software before it ever reaches the end-user, bypassing many conventional security measures.
The reliance on open-source software, while a cornerstone of contemporary development, introduces a unique set of security challenges. The collaborative nature of open-source projects means that contributions come from a vast, often anonymous, global community. While this fosters innovation, it also creates opportunities for malicious actors to introduce vulnerabilities or directly embed malware. High-profile incidents like the SolarWinds attack in 2020, which leveraged a compromised software update to infiltrate numerous government agencies and corporations, brought the severity of supply chain attacks into sharp focus. The LiteLLM case, targeting a popular AI development tool, underscores that no sector, particularly one as critical and rapidly evolving as AI, is immune. The implications for trust in the foundational tools used to build AI systems are significant, potentially slowing innovation as developers become more cautious about integrating external components.
The Irony of Compliance: Delve’s Role Under the Microscope
Adding a complex layer of intrigue to the LiteLLM saga is the revelation regarding its security compliance certifications. As of late March, LiteLLM prominently displayed on its website that it had successfully passed two major security compliance audits: SOC 2 and ISO 27001. These certifications are widely recognized benchmarks, intended to assure stakeholders that an organization has robust security policies, processes, and controls in place to protect sensitive data and manage risks. SOC 2 (Service Organization Control 2) focuses on a company’s non-financial reporting controls related to security, availability, processing integrity, confidentiality, and privacy. ISO 27001, an international standard, specifies requirements for establishing, implementing, maintaining, and continually improving an information security management system (ISMS). While these certifications do not guarantee absolute immunity from cyberattacks, they signify a commitment to a structured and proactive approach to security.
The controversy arises because LiteLLM obtained these certifications through Delve, a startup that positions itself as an AI-powered compliance provider, also a Y-Combinator alumnus. Delve has recently faced a series of serious allegations. Reports suggest the company has been accused of misleading its customers regarding their true compliance posture by allegedly generating fabricated data and utilizing auditors who merely "rubber-stamp" reports without conducting thorough due diligence. Delve has vehemently denied these allegations, asserting the integrity of its services and processes.
The juxtaposition of LiteLLM’s malware incident with the allegations against Delve has ignited considerable debate within the tech community. Social media platforms, particularly X (formerly Twitter), became a forum for discussions and observations, with many questioning the value of certifications if the underlying security practices are compromised or if the certifying body itself lacks credibility. As one engineer noted, the coincidence felt like a "joke" given the context. This situation highlights a critical distinction: certifications attest to the existence and operation of security controls and policies, not to the absence of vulnerabilities or the prevention of all future incidents. However, for a company that has invested in and publicly showcased such certifications to be breached, especially through a common vector like a supply chain attack that SOC 2 is supposed to address, raises legitimate questions about the depth and effectiveness of the certified controls.
Navigating the Complexities of Digital Trust and Compliance
The LiteLLM incident and the concurrent scrutiny of Delve illuminate broader challenges within the technology sector concerning digital trust and the evolving landscape of compliance. In an era where digital transformation is accelerating across all industries, the demand for robust security assurances has skyrocketed. Businesses, particularly those engaging with enterprise clients, often find SOC 2 or ISO 27001 certifications to be non-negotiable requirements. This has fueled the rise of "compliance-as-a-service" providers, promising faster, more efficient pathways to certification. While beneficial in theory, this model can inadvertently foster a culture of "compliance theater," where the emphasis shifts from genuine security enhancement to merely obtaining a badge for marketing purposes.
Neutral analytical commentary suggests that true security goes beyond a checklist. It requires a continuous, adaptive process of risk assessment, vulnerability management, and incident response. Even with certifications, organizations must remain vigilant, understanding that the threat landscape is constantly shifting. For open-source projects, the challenge is particularly acute. The collaborative model, while powerful for innovation, decentralizes responsibility, making comprehensive security audits more complex. Developers must increasingly scrutinize their dependencies, employing tools for software composition analysis and maintaining strict version control.
The market and social impact of such incidents are multifaceted. For developers, there may be increased apprehension about integrating open-source components, potentially slowing down development cycles as more rigorous vetting becomes necessary. For businesses relying on AI tools, the incident underscores the imperative of due diligence, not only on the tools themselves but also on the security practices of their providers and the credibility of their compliance claims. Culturally, it reinforces the ongoing tension between the "move fast and break things" ethos, which has historically driven Silicon Valley, and the growing demand for stability, reliability, and robust security.
Looking Ahead: Rebuilding Trust in the AI Ecosystem
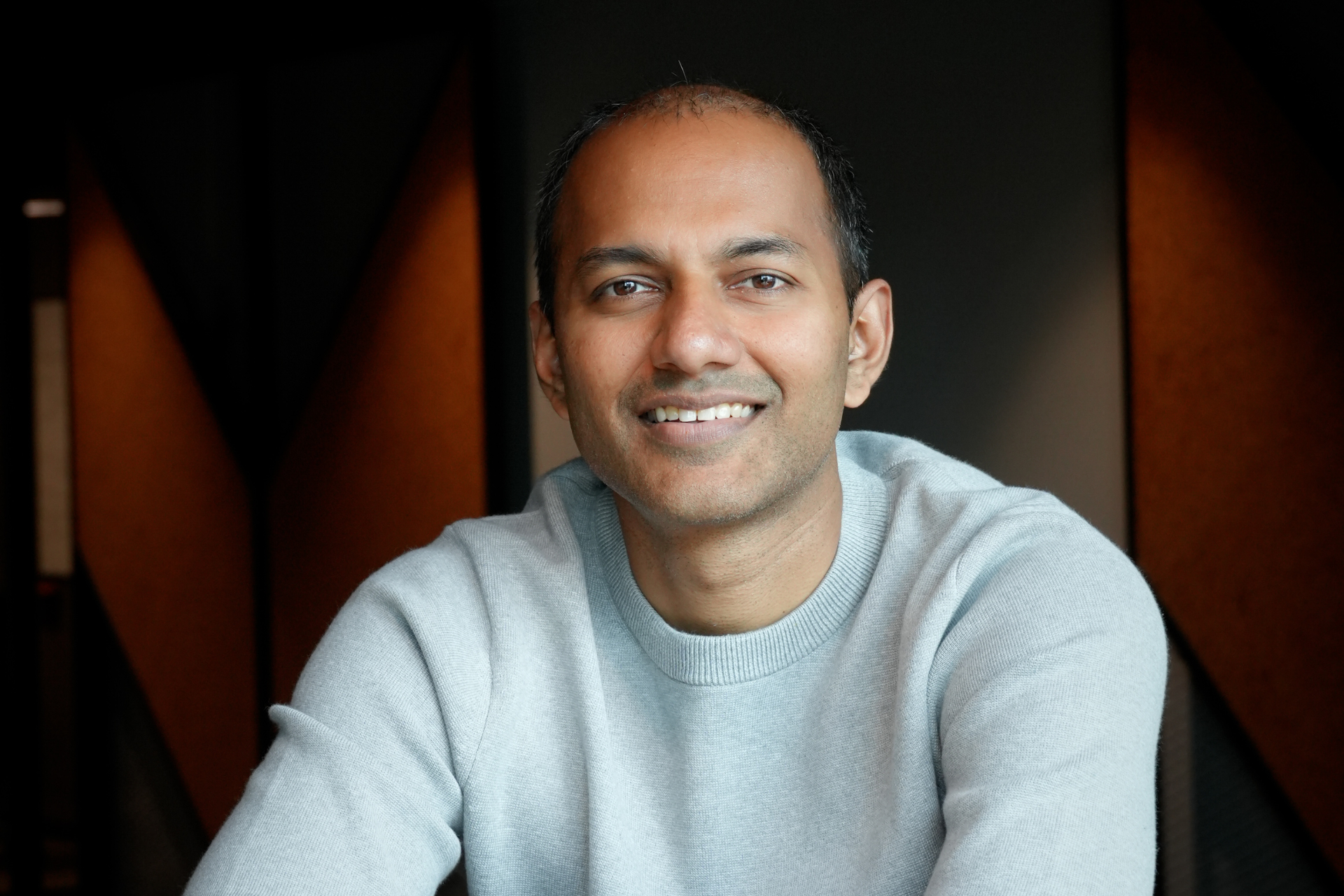
As LiteLLM continues its investigation in collaboration with cybersecurity experts like Mandiant, the focus remains on understanding the full scope of the breach and implementing comprehensive remediations. CEO Krrish Dholakia has emphasized the company’s commitment to sharing "technical lessons learned" with the developer community once their forensic review is complete, a move that could contribute significantly to collective cybersecurity knowledge.
This incident serves as a critical inflection point for the AI community and the broader tech industry. It underscores the urgent need for heightened vigilance in software supply chain security, pushing developers and organizations to adopt more proactive measures to vet and monitor their dependencies. Simultaneously, it prompts a crucial reevaluation of security compliance mechanisms, questioning whether current certification processes adequately reflect and address the dynamic and complex realities of modern cyber threats. Ultimately, rebuilding and maintaining digital trust in the rapidly evolving AI ecosystem will depend not just on innovative technology, but on a collective, unwavering commitment to robust security practices and transparent accountability.