A sophisticated and user-friendly exploit kit, previously employed in targeted state-sponsored cyberattacks, has been publicly disseminated on the code-sharing platform GitHub, sparking widespread alarm among cybersecurity experts. This critical development means that a newer iteration of the advanced hacking tool, known as DarkSword, is now accessible to a vastly wider array of malicious actors, significantly expanding the threat landscape for potentially hundreds of millions of iPhone and iPad users who have not updated their devices to the latest operating system. The ease with which this exploit can be deployed eliminates the need for specialized iOS hacking expertise, presenting an unprecedented risk of mass exploitation.
The initial discovery of the DarkSword campaign surfaced just last week when cybersecurity researchers identified its use in a targeted hacking operation against iPhone users. This earlier variant was already considered highly advanced, capable of breaching device security with considerable stealth. The subsequent public release of an updated version on GitHub, however, escalates the situation from a contained, albeit serious, threat to a pervasive digital vulnerability. Experts are now cautioning that any individual with basic technical proficiency can readily adapt and utilize these tools, turning them against unsuspecting users worldwide.
The Anatomy of DarkSword: A Sophisticated Threat Made Simple
DarkSword is categorized as an exploit kit, a collection of tools and code designed to take advantage of specific software vulnerabilities. In this instance, it targets weaknesses in older versions of Apple’s iOS operating system. Matthias Frielingsdorf, co-founder of mobile security startup iVerify, expressed profound concern regarding the leak, stating that the exploits are "way too easy to repurpose" and that their proliferation "cannot be contained anymore." He anticipates a rapid uptake by cybercriminals and other nefarious entities.
Frielingsdorf and his colleagues at iVerify had previously analyzed earlier versions of DarkSword spyware. He noted that while the newly leaked files share the underlying infrastructure with those previously examined, there are slight differences in their composition. Crucially, the files uploaded to GitHub are remarkably straightforward, consisting primarily of HTML and JavaScript. This simplicity means that the barrier to entry for potential attackers is exceptionally low; an attacker could, theoretically, copy, paste, and host these files on a server within a matter of minutes to a few hours. The exploits are designed to function "out of the box," eliminating the requirement for in-depth iOS expertise, a characteristic that makes this leak particularly dangerous.
This assessment was corroborated by Kimberly Samra, a spokesperson for Google, whose researchers had also previously conducted an in-depth analysis of the DarkSword exploit chain. Their findings align with Frielingsdorf’s grave appraisal of the situation. Further underscoring the immediate threat, a security hobbyist operating under the handle "matteyeux" publicly demonstrated the exploit’s ease of use. Matteyeux reported on X (formerly Twitter) that they successfully hacked an iPad mini running iOS 18, a previous generation of the operating system known to be vulnerable to DarkSword, using the "in the wild" samples now circulating online. This real-world validation of the exploit’s functionality highlights the immediate and tangible danger posed by the public leak.
The leaked code itself provides chilling insights into DarkSword’s capabilities. Contained within are several comments, likely left by its original developers, that detail its operational mechanics and implementation instructions. One comment explicitly states that the exploit "reads and exfiltrates forensically-relevant files from iOS devices via HTTP." This refers to the systematic theft of sensitive information from a compromised iPhone or iPad, with the data then transmitted over the internet to a server controlled by the attacker. Such "forensically-relevant files" typically include an individual’s contacts, messages, call history, and even the iOS keychain, which securely stores Wi-Fi passwords, authentication tokens, and other critical secrets. Another section of the code references "post-exploitation activity," outlining the processes undertaken once the malware has gained initial access, detailing how it comprehensively harvests the device’s contents before dumping them to a remote server. Interestingly, one file also contains references to uploading data to a popular Ukrainian apparel website, though the exact reason for this remains unclear.
The Vast Scale of Vulnerability
The threat posed by DarkSword is not confined to a niche group of users; it extends to a significant portion of Apple’s global device ecosystem. According to Apple’s own publicly available data, approximately one-quarter of all active iPhone and iPad users are currently running iOS 18 or an even older version of the operating system. Considering that Apple reported more than 2.5 billion active devices globally as of early 2026, this translates into a staggering number—potentially over 625 million devices—that are now vulnerable to DarkSword attacks.
This substantial user base on older operating systems can be attributed to several factors. Many users might possess older hardware that no longer supports the very latest iOS versions. Others may simply not prioritize software updates, perhaps due to perceived stability issues with new releases, concerns about battery life, or a lack of awareness regarding the critical security implications of outdated software. Some users might also face storage limitations that prevent them from downloading large update files, or they may simply forget to install updates when prompted. Regardless of the reason, this "patch gap" creates a fertile ground for exploits like DarkSword.
Apple spokesperson Sarah O’Rourke acknowledged the company’s awareness of the exploit targeting devices running older, out-of-date operating systems. In response to such threats, Apple had already issued an emergency security update on March 11, specifically designed for devices that are unable to run the very latest versions of iOS. O’Rourke emphatically reiterated Apple’s standing advice: "Keeping your software up to date is the single most important thing you can do to maintain the security of your Apple products." She further clarified that devices running updated software are not susceptible to these particular reported attacks. Additionally, Apple’s "Lockdown Mode," an extreme security feature designed for individuals who might be targets of highly sophisticated cyberattacks, would also effectively block these specific DarkSword exploits. Despite these protective measures, the sheer volume of unpatched devices represents a formidable challenge.
A Troubling Trend: The Proliferation of State-Grade Cyberweapons
The public leak of DarkSword is not an isolated incident but rather part of a disturbing trend involving the proliferation of advanced cyber-espionage tools. Only weeks prior to the DarkSword revelation, researchers uncovered another sophisticated iPhone hacking toolkit known as Coruna. As reported, Coruna was allegedly developed by the defense contractor L3Harris, specifically by its Trenchant division, which specializes in creating hacking tools for the U.S. government and its allies. This highlights a broader, often opaque, "gray market" for cyberweapons, where tools initially designed for state-level intelligence gathering or law enforcement purposes can eventually leak or be repurposed.
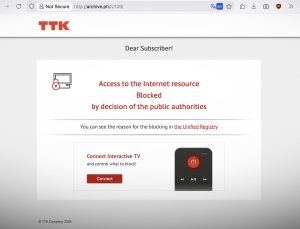
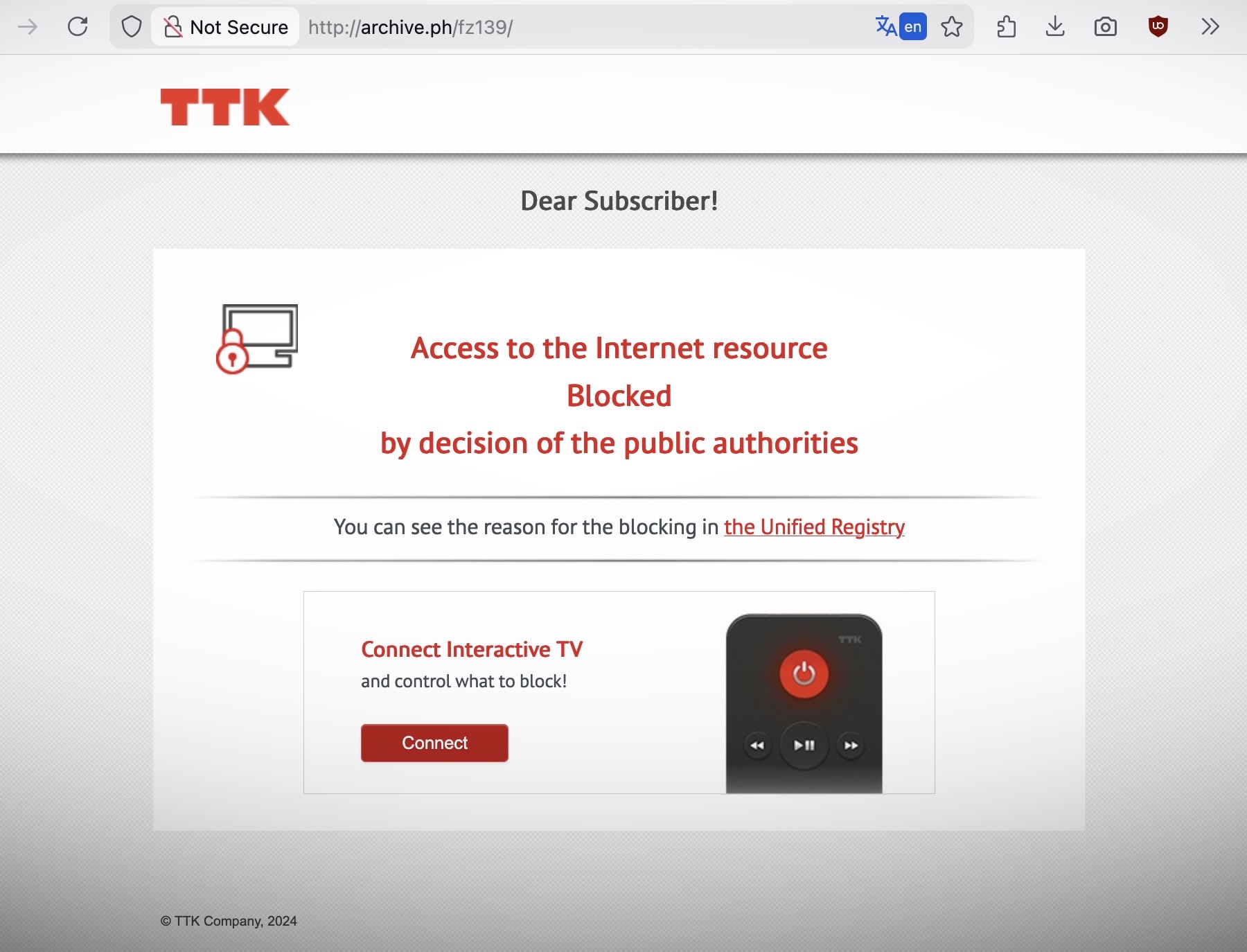
The alleged origins of DarkSword itself point to state sponsorship, with reports indicating its use by Russian government hackers targeting Ukrainian individuals. This context underscores the geopolitical dimensions of cybersecurity, where sophisticated tools developed in the shadows of national security operations can, through various means, find their way into the hands of criminal organizations or other hostile entities. The "dual-use" nature of these technologies—designed for legitimate national security applications but easily weaponized for nefarious purposes—presents a profound ethical and practical dilemma for both governments and the private sector. The leakage of such tools effectively democratizes advanced hacking capabilities, lowering the bar for entry into sophisticated cybercrime and dramatically increasing the potential for widespread harm.
GitHub’s Conundrum: Balancing Open Source with Security
The publication of the DarkSword exploit on GitHub, a platform owned by Microsoft and renowned as a hub for open-source development and code collaboration, presents a complex challenge. GitHub’s mission promotes open access to code, fostering innovation and collaboration. However, this ethos inevitably clashes with the imperative to prevent the dissemination of actively malicious tools that can cause significant real-world harm.
For platforms like GitHub, the decision to remove or restrict access to code that could be used for illicit purposes is fraught with ethical and practical difficulties. While the original article noted that a Microsoft spokesperson did not immediately respond to a request for comment, such platforms typically grapple with policies surrounding the identification and moderation of potentially harmful content, balancing freedom of information with responsibility for public safety. The "uncontainable" nature of the exploit, as described by Frielingsdorf, suggests that once such code is released into the wild, even its removal from the initial hosting platform may not prevent its continued circulation across the internet. This incident reignites debates within the cybersecurity community about responsible disclosure, the ethics of publishing exploits, and the role of platforms in managing potentially dangerous content.
Immediate Action and Long-Term Implications
Given the gravity of the situation, the most immediate and critical recommendation for all iPhone and iPad users is to update their operating systems to the very latest version of iOS. This action patches the underlying vulnerabilities that DarkSword exploits, effectively rendering the attack ineffective. Users should also ensure that automatic updates are enabled on their devices to mitigate future risks. For those with older devices that cannot support the newest iOS versions, installing any available emergency security updates, as released by Apple on March 11, is paramount.
Beyond immediate updates, users are advised to adopt a holistic approach to digital security. Enabling Apple’s Lockdown Mode, if applicable and appropriate for their risk profile, provides an additional layer of defense. Practicing good cyber hygiene, such as using strong, unique passwords, enabling two-factor authentication, and exercising extreme caution when clicking on unfamiliar links or opening attachments, remains essential.
For the technology industry, the DarkSword leak underscores the relentless cat-and-mouse game between attackers and defenders. It places renewed pressure on device manufacturers like Apple to not only accelerate the patching of vulnerabilities but also to potentially re-evaluate their support lifecycles for older devices, recognizing the vast number of users who continue to rely on them. Furthermore, it highlights the continuous need for investment in advanced threat intelligence and proactive security measures to stay ahead of sophisticated adversaries, whether they are state-sponsored or newly empowered criminal groups.
In conclusion, the public release of the DarkSword exploit kit marks a critical juncture in mobile cybersecurity. It transforms a targeted threat into a widespread danger, placing millions of unpatched iPhone and iPad users at immediate risk. While Apple has provided crucial updates and advice, the burden now falls heavily on individual users to take prompt action to secure their devices. This event serves as a stark reminder of the ever-present and evolving nature of cyber threats in our increasingly interconnected digital world.