A significant cybersecurity incident in 2023 saw an unidentified foreign actor penetrate the Federal Bureau of Investigation’s New York field office network, subsequently gaining access to sensitive documents related to the bureau’s high-profile investigation into convicted sex offender Jeffrey Epstein. The intrusion, detailed in reports citing internal sources and court records, represents a concerning compromise of a leading U.S. law enforcement agency’s digital infrastructure and raises profound questions about national security and the integrity of ongoing criminal investigations.
The Mechanics of the Intrusion
The breach reportedly exploited a vulnerability within a server located at the Child Exploitation Forensic Lab, a critical component of the FBI’s New York Field Office operations. This server was inadvertently left exposed to external threats by an FBI special agent involved in the Epstein case, creating an unforeseen entry point for the foreign hacker. According to court documents referenced in the reports, the intruder "combed through certain files pertaining to the Epstein investigation," indicating a targeted or at least opportunistic exploration of highly sensitive data once inside the network. What makes this incident particularly unusual, according to a source close to the investigation, is that the hacker reportedly remained unaware they had successfully infiltrated the FBI’s systems until confronted by agents during a video call, where the federal officers revealed their identities and credentials. This detail suggests a potential lack of sophistication in the attacker’s initial reconnaissance or an underestimation of the target, yet still underscores a critical lapse in federal cybersecurity defenses.
The Shadow of the Epstein Investigation
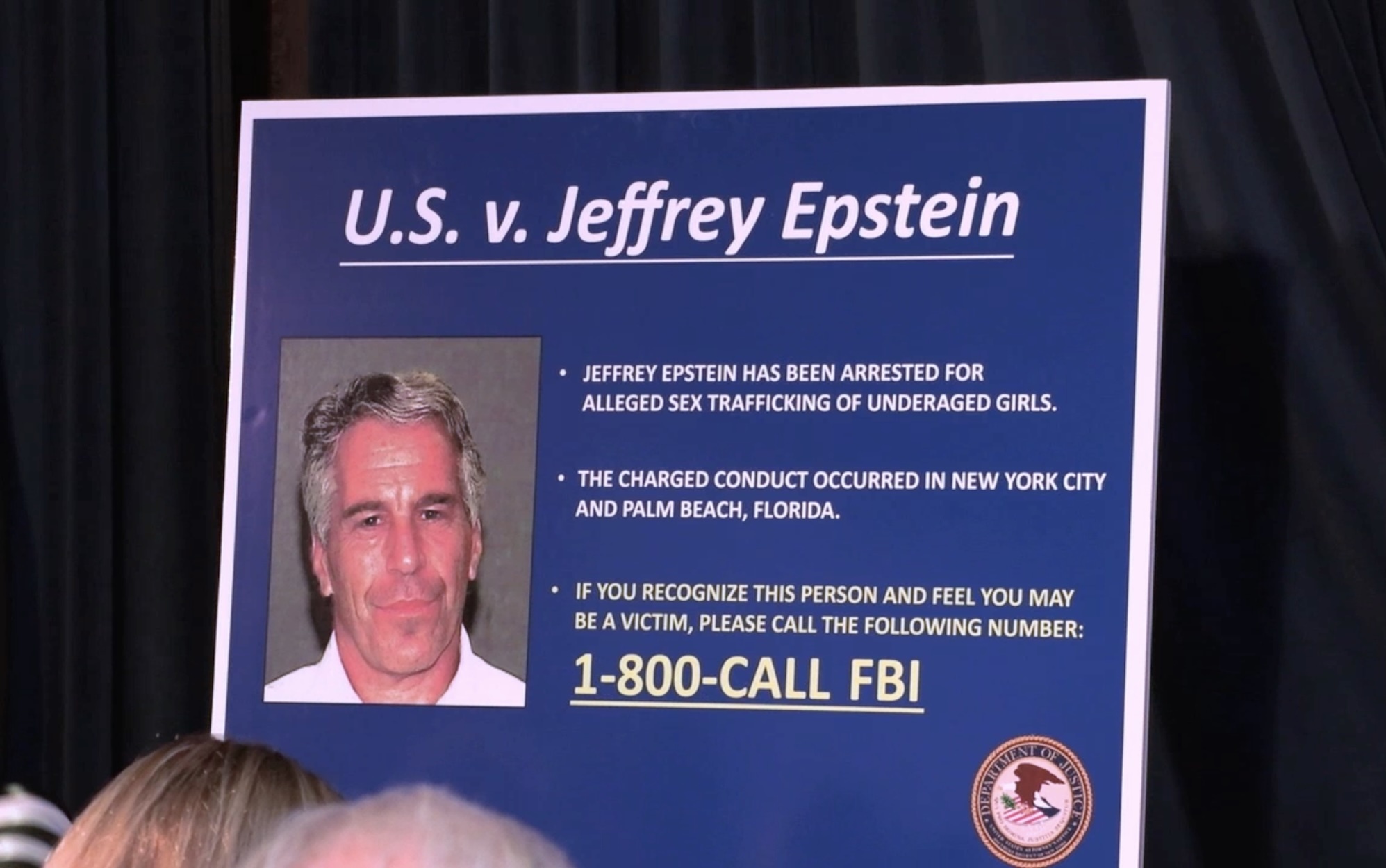
The files compromised in this breach are linked to the federal investigation of Jeffrey Epstein, a financier whose criminal activities and death in federal custody ignited widespread public outrage and fueled numerous conspiracy theories. Epstein’s history of sex trafficking and abuse, particularly involving underage girls, spanned decades and involved a network of powerful and influential individuals. His 2008 plea deal in Florida, which many viewed as unduly lenient, sparked considerable controversy, leading to renewed federal scrutiny and a subsequent indictment in 2019. Epstein’s death by suicide in a Manhattan jail cell while awaiting trial intensified public and media attention, prompting calls for greater transparency and accountability regarding his alleged co-conspirators and the handling of his case.
The FBI’s ongoing investigation into Epstein’s associates and the broader sex trafficking ring is immensely complex, involving numerous victims, potential witnesses, and a vast collection of evidence. Any compromise of these files, whether related to victim identities, witness statements, investigative strategies, or evidence collected, carries substantial risks. It could potentially jeopardize the safety of individuals involved, undermine prosecutorial efforts, or even provide intelligence to those seeking to obstruct justice. The public’s deep-seated desire for answers regarding Epstein’s network and accountability for those complicit means that any perceived vulnerability or interference with the investigation is met with intense scrutiny and concern.
National Security and Public Confidence Implications
A breach of this nature at a federal law enforcement agency like the FBI reverberates beyond the immediate compromise of data. It directly impacts national security by potentially exposing sensitive investigative techniques, intelligence sources, and the identities of agents or informants. While the FBI spokesperson stated the incident was isolated and contained, the very fact that a foreign actor could penetrate such a critical system raises alarms. It suggests a potential vulnerability that, if not fully understood and mitigated, could be exploited by more sophisticated state-sponsored actors seeking to gather intelligence, disrupt operations, or sow discord.
Furthermore, the incident erodes public confidence in the government’s ability to safeguard highly sensitive information. In an era where digital data underpins nearly every aspect of governance and law enforcement, citizens expect federal agencies to maintain robust cybersecurity defenses. The FBI, as a premier investigative body, is entrusted with protecting the nation from myriad threats, including cyber espionage and crime. A breach of its own internal systems, particularly one attributed to an inadvertent oversight, can foster skepticism and distrust, making it harder for the agency to gain public cooperation and maintain its authority. The specific context of the Epstein investigation, already fraught with public mistrust and suspicion, amplifies these concerns, feeding into narratives of systemic failure or even deliberate obfuscation.
A Wider View: Government Cybersecurity Under Siege
The breach at the FBI’s New York field office is not an isolated incident but rather a stark reminder of the persistent and evolving cyber threats facing government institutions globally. Over the past two decades, numerous high-profile cyberattacks have targeted U.S. federal agencies, highlighting the constant battle between digital defenders and malicious actors. Instances such as the 2015 breach of the Office of Personnel Management (OPM), which exposed the personal data of millions of federal employees and contractors, or the 2020 SolarWinds supply chain attack, which infiltrated multiple federal agencies, underscore the pervasive nature of these threats.
These attacks often originate from a diverse range of actors, including state-sponsored groups engaged in espionage or sabotage, financially motivated criminal organizations, and even ideologically driven hacktivists. The motivations are varied, ranging from intelligence gathering and intellectual property theft to disrupting critical infrastructure or undermining democratic processes. Government networks, by their very nature, house invaluable data—from classified intelligence and national security secrets to personal information of citizens and details of ongoing criminal investigations—making them prime targets. The "human element" often plays a critical role in these vulnerabilities, as seen in the FBI incident where an agent’s oversight reportedly created the entry point. This highlights the need for not just advanced technological defenses but also continuous, rigorous training and adherence to strict security protocols by all personnel with network access.
The FBI’s Containment and Ongoing Inquiry
In the immediate aftermath of the cyber incident, an FBI spokesperson issued a statement acknowledging the breach. "Following the 2023 cyber incident, the FBI contained the affected network and determined the incident to be an isolated one," the spokesperson confirmed, adding that "The FBI restricted access to the malicious actor and rectified the network." This swift containment and remediation effort is standard procedure in response to such breaches, aiming to prevent further data exfiltration or system compromise. However, the designation of the incident as "isolated" and the network as "rectified" typically refers to the immediate technical response and does not necessarily diminish the gravity of the initial intrusion or the potential long-term implications of the data accessed.
The FBI emphasized that its investigation into the breach remains ongoing. This ongoing inquiry is crucial not only to fully understand the extent of the compromise and what specific information was accessed but also to identify the perpetrator and their motivations. Federal investigations into cyberattacks are often complex and protracted, involving digital forensics, intelligence gathering, and international cooperation. The FBI will be working to ascertain if the foreign actor was operating independently or as part of a larger state-sponsored or criminal enterprise, and whether the compromise of Epstein-related files was a primary objective or an opportunistic discovery. Any potential disciplinary actions for the agent whose oversight led to the vulnerability would likely be handled internally, consistent with federal agency protocols.
Strengthening Defenses Against Evolving Threats
The FBI breach serves as a powerful call to action for all government agencies to re-evaluate and enhance their cybersecurity postures. In an increasingly interconnected world, where cyber threats are constantly evolving in sophistication and frequency, a multi-layered defense strategy is imperative. This includes not only investing in cutting-edge cybersecurity technologies—such as advanced threat detection systems, encryption, and secure network architectures—but also fostering a robust "culture of security" among all employees. Regular training, strict adherence to security protocols, and prompt patching of vulnerabilities are critical to mitigating the risk posed by both external attackers and internal human error.
Furthermore, collaboration and intelligence sharing among federal agencies, as well as with international partners and the private sector, are essential in staying ahead of cyber adversaries. Understanding emerging threats, sharing indicators of compromise, and collectively developing defensive strategies can create a more resilient digital infrastructure for the nation. The incident involving the Epstein files within the FBI’s network underscores that no institution, regardless of its mission or security protocols, is entirely immune to cyber intrusion. It is a continuous, dynamic battle that demands constant vigilance, adaptation, and a proactive approach to protecting sensitive information vital to national security and public trust.