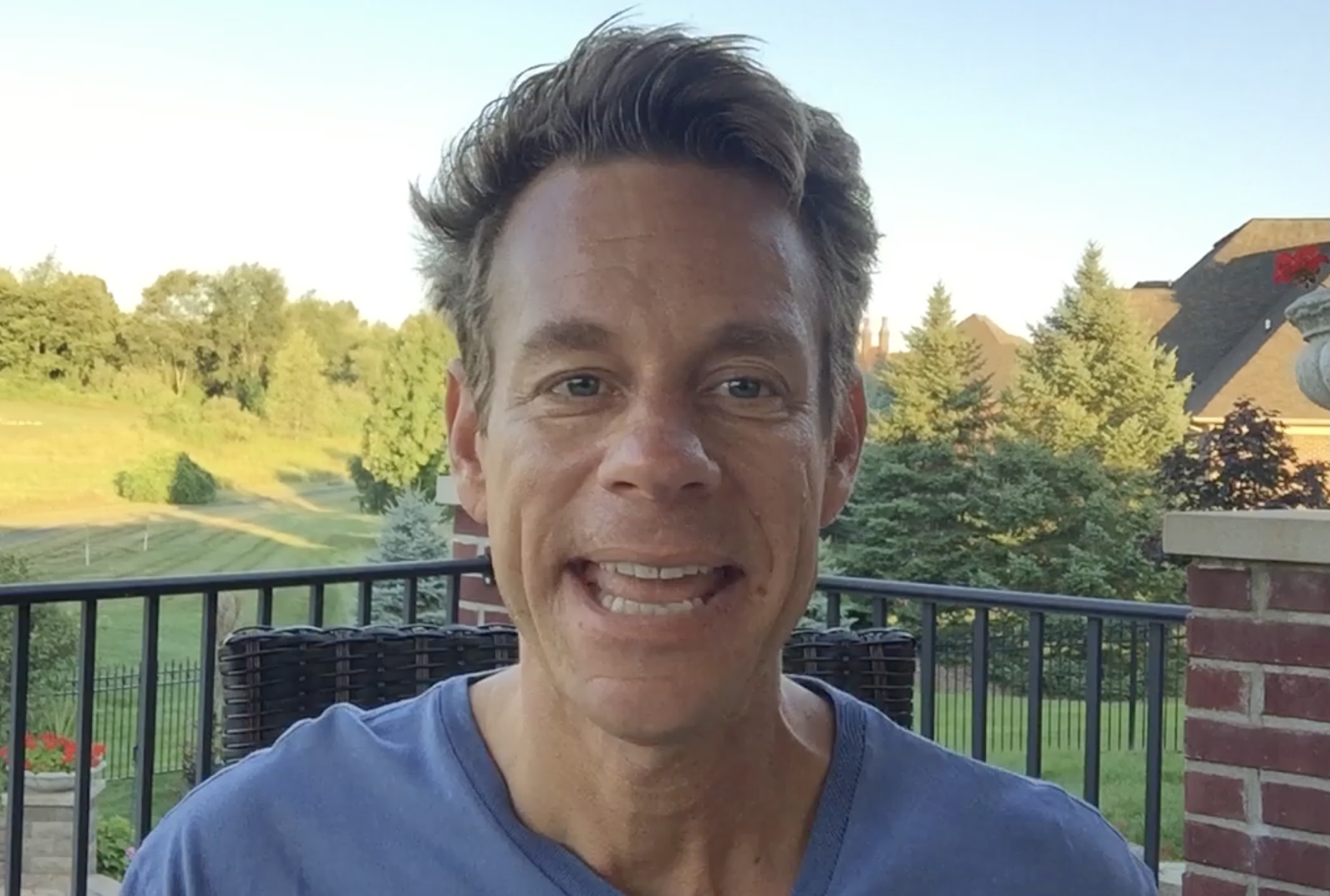
Bryan Fleming, the founder of pcTattletale, a company widely recognized for its controversial surveillance software, has been spared incarceration following his guilty plea to U.S. federal charges. The sentencing, which occurred on Friday in a San Diego federal court, concluded a years-long investigation, marking the first successful prosecution of a spyware developer by the U.S. Department of Justice in over a decade. Fleming received a sentence of time served and a $5,000 monetary fine, a decision confirmed by a spokesperson for the U.S. Attorney for the Southern District of California, the office responsible for bringing the charges.
The outcome of this case, particularly the absence of a custodial sentence despite Fleming’s admission to creating, distributing, and marketing spyware for illicit purposes, has sparked considerable discussion within legal and cybersecurity circles. Prosecutors themselves had previously advocated for no jail time or fine, a stance that raises questions about the complexities of prosecuting digital surveillance crimes and the evolving legal landscape surrounding privacy in the digital age.
Understanding the Landscape of Stalkerware
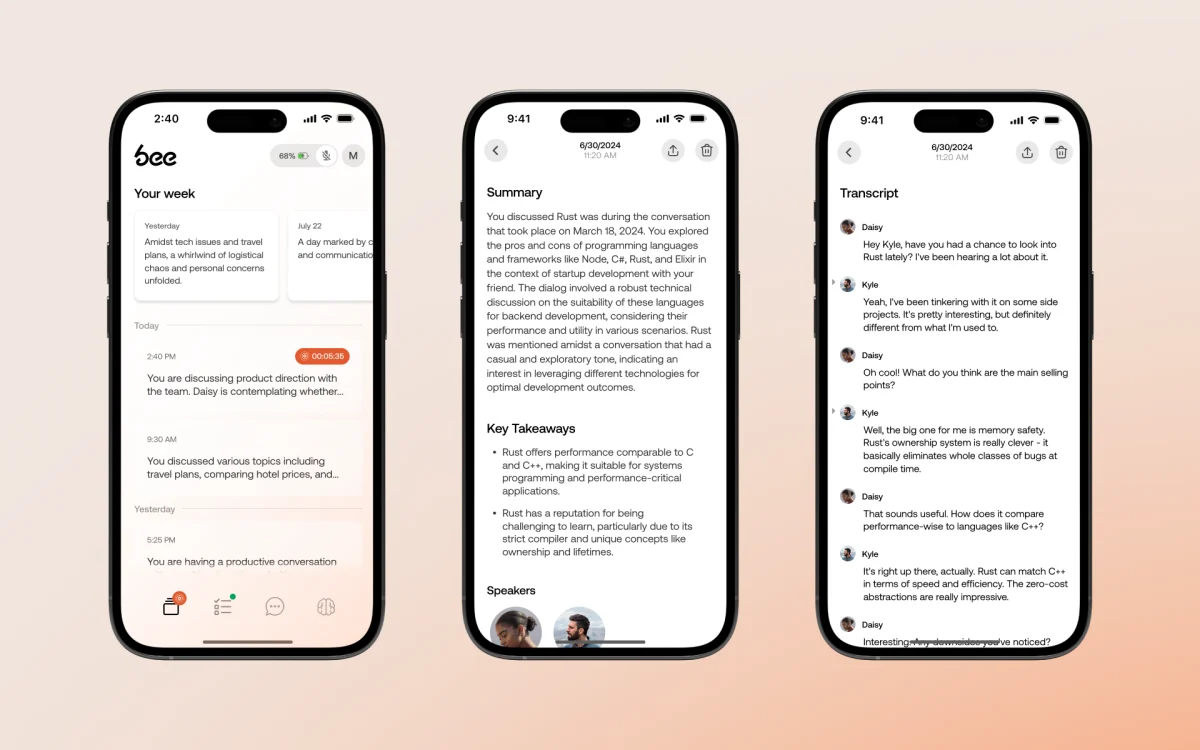
At the heart of the prosecution against Bryan Fleming was his company, pcTattletale, which specialized in what is commonly known as "stalkerware" or "consumer-grade spyware." These applications are insidious tools designed to be covertly installed on a person’s digital device, such as a computer or smartphone, without their knowledge or consent. Once installed, the software operates stealthily in the background, continuously monitoring and uploading a vast array of the victim’s private data to a remote server accessible by the perpetrator. This data often includes personal messages, photographs, browsing history, real-time location data, and even keystrokes, effectively turning the victim’s device into a personal surveillance portal.
The proliferation of stalkerware represents a significant threat to individual privacy and digital security. While often marketed under the guise of parental control or employee monitoring tools, their true utility frequently lies in facilitating non-consensual surveillance, particularly in cases of domestic abuse. Experts and advocacy groups consistently highlight how these tools empower abusers, enabling them to track, harass, and control victims, thereby escalating patterns of emotional and physical violence. The ease of access, relatively low cost, and often sophisticated concealment mechanisms of these apps make them a dangerous weapon in the hands of perpetrators, creating a pervasive sense of fear and isolation for those targeted.
A Decade-Long Pursuit: The Road to Conviction
The federal investigation into Bryan Fleming and pcTattletale was initiated by Homeland Security Investigations (HSI), a critical unit within U.S. Immigration and Customs Enforcement, as part of a broader crackdown on the consumer-grade spyware industry. Charges were formally brought against Fleming in 2025. Unlike many other spyware operators who conduct their business from international jurisdictions, placing them beyond the immediate reach of U.S. law enforcement, Fleming operated and facilitated the use of his spyware directly from within the United States. This crucial detail made him a viable target for federal agents and ultimately led to his apprehension and prosecution.
During a plea hearing in January of the current year, which followed a rigorous, multi-year federal probe, Fleming formally admitted his culpability. He confessed to developing, selling, and actively promoting spyware for applications that were unequivocally unlawful. Federal investigators, in an affidavit filed to secure a search warrant for his residence, specifically asserted that Fleming had, in numerous instances, "knowingly assisted customers seeking to spy on nonconsenting, non-employee adults." This direct acknowledgment of his complicity in illegal surveillance underscored the severity of the charges he faced and the breach of privacy his software enabled.
The extent of pcTattletale’s reach and the number of individuals it victimized remain largely unknown. However, a significant data breach in 2024 provided a chilling glimpse into the scale of the company’s long-running operation. An independent security researcher uncovered a critical vulnerability within pcTattletale’s systems, which inadvertently exposed millions of screen captures. These images, meticulously recorded by the spyware from victims’ devices every few seconds, were openly accessible on the internet, allowing anyone to view the contents of countless computer displays. Disturbingly, this exposed data included screenshots from check-in computers at several U.S. hotels where pcTattletale had been installed, revealing sensitive guest and reservation details. Fleming reportedly failed to respond to the researcher’s warnings or rectify the critical security flaw.
Just one week after this exposé, pcTattletale abruptly ceased its operations in 2024, following a high-profile cyberattack, website defacement, and a more extensive data breach. The hacker responsible for this breach claimed to have exploited a separate security vulnerability, gaining full access to all files stored within pcTattletale’s cloud data storage account, including extensive victim data. This incident unveiled that over 138,000 customers had utilized the company’s services to surveil an untold number of individuals. Fleming, at the time, informed reporters that he had "deleted everything" from his company’s servers in the wake of the breach, but there is no indication that he notified either his customers or their victims of the compromise.
The Sentence and Its Implications
The sentencing of Bryan Fleming to "time served" and a modest $5,000 fine, particularly after prosecutors recommended against a custodial sentence, has ignited a debate about the effectiveness of current legal frameworks in addressing cybercrimes and holding perpetrators accountable. While the conviction itself is a significant milestone, being the first of its kind in over ten years, the leniency of the penalty raises questions about its potential impact as a deterrent.
Legal experts suggest several factors could influence such a sentencing decision. These might include Fleming’s cooperation with investigators, the absence of prior convictions, or the perceived difficulty in proving direct malicious intent for every single user of his software. Furthermore, the nascent and complex nature of prosecuting digital surveillance crimes often presents judges with challenging precedents. Unlike traditional crimes, the "weapon" is code, the "crime scene" is virtual, and the "injury" is often an intangible violation of privacy, making traditional sentencing guidelines sometimes difficult to apply.
Critics argue that a non-custodial sentence, coupled with a relatively small fine, might not adequately reflect the profound harm inflicted upon victims of stalkerware. The psychological trauma, erosion of trust, and potential for real-world danger that these tools enable are substantial. A lenient sentence, some contend, could inadvertently send a message that the legal system does not fully grasp or sufficiently punish the gravity of digital privacy violations, potentially failing to deter other developers from entering or continuing in the illicit spyware market. Conversely, proponents of the sentence might argue that the conviction itself, regardless of the penalty, establishes a critical precedent that the U.S. Department of Justice is actively pursuing and successfully prosecuting these cases, thereby signaling a shift in enforcement strategy.
A Wider Battle Against Digital Surveillance
The demise of pcTattletale and Fleming’s conviction are not isolated incidents but rather part of a larger trend in the ongoing struggle against consumer-grade spyware. Over recent years, several other prominent stalkerware providers, including LetMeSpy, Cocospy, and Spyhide, have also been forced offline or shuttered their operations following security lapses, data breaches, or increased scrutiny from law enforcement and privacy advocates. These events highlight a growing vulnerability within the stalkerware industry itself, where the very tools designed to exploit others’ privacy often fall prey to their own security deficiencies.
This pattern underscores the critical role played by independent security researchers and ethical hackers. Their efforts in identifying and publicly disclosing vulnerabilities in these surveillance apps often serve as the initial catalyst for investigations, public awareness, and, ultimately, the downfall of these operations. Without their persistent work, many of these illicit activities might continue undetected, further endangering countless individuals.
The Market and Societal Cost of Stalkerware
The market for stalkerware, despite its ethical and legal ambiguities, remains robust due to persistent demand driven by various motives, ranging from legitimate (though often misguided) parental concerns to malicious intent in abusive relationships. Companies like pcTattletale frequently cloak their marketing in terms of "child safety" or "employee productivity," deliberately blurring the lines between legitimate monitoring and illicit surveillance. This rhetorical strategy often enables them to operate in a legal "gray area," exploiting loopholes and societal anxieties.
The societal cost of stalkerware is immense. It erodes fundamental trust in personal relationships, fuels domestic violence, and undermines the basic right to privacy. Victims often experience severe psychological distress, including paranoia, anxiety, and a feeling of constant violation. Furthermore, the sensitive nature of the data collected—financial information, intimate communications, and location data—exposes victims to risks far beyond emotional trauma, including identity theft, blackmail, and physical harm.
Looking Ahead: Enforcement and Prevention
Bryan Fleming’s conviction represents a significant, albeit complex, step forward in the fight against illegal digital surveillance. While the specific sentence may invite debate, the very act of a federal prosecution and conviction sets a crucial precedent. It signals that U.S. law enforcement agencies are increasingly equipped and determined to pursue developers and distributors of these intrusive tools, even as many continue to operate from overseas.
However, the challenges remain formidable. The global nature of the internet, coupled with the rapid evolution of technology, means that new forms of surveillance software are constantly emerging. Effective countermeasures will require a multi-pronged approach: strengthening existing privacy laws, fostering international cooperation among law enforcement agencies, increasing public awareness about the dangers of stalkerware, and investing in cybersecurity education. Ultimately, protecting individuals from the insidious creep of digital surveillance demands a continuous and concerted effort from legal systems, technology companies, and society as a whole.